Create an SSL Certificate on Apache for CentOS
hostname set-hostname <name server>
Step 1 — Installing mod_ssl
In order to set up the self-signed certificate, you first have to be sure that mod_ssl, an Apache module that provides support for SSL encryption, is installed on the server. You can install mod_ssl with the yum command:
sudo yum install mod_ssl openssl
Copy
The module will automatically be enabled during installation, and Apache will be able to start using an SSL certificate after it is restarted. You don’t need to take any additional steps for mod_ssl to be ready for use.
Step 2 — Creating a New Certificate
Now that Apache is ready to use encryption, you can move on to generating a new SSL certificate. TLS/SSL works by using a combination of a public certificate and a private key. The SSL key is kept secret on the server. It is used to encrypt content sent to clients. The SSL certificate is publicly shared with anyone requesting the content. It can be used to decrypt the content signed by the associated SSL key.
The /etc/ssl/certs directory, which can be used to hold the public certificate, should already exist on the server. You will need to create an /etc/ssl/private directory as well, to hold the private key file. Since the secrecy of this key is essential for security, it’s important to lock down the permissions to prevent unauthorized access:
sudo mkdir /etc/ssl/private
sudo chmod 700 /etc/ssl/private
Copy
Now, you can create a self-signed key and certificate pair with OpenSSL in a single command by typing:
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/apache-selfsigned.key -out /etc/ssl/certs/apache-selfsigned.crt
Copy
You will be asked a series of questions. Before going over that, let’s take a look at what is happening in the command:
- openssl: This is the basic command line tool for creating and managing OpenSSL certificates, keys, and other files.
- req: This subcommand specifies that you want to use X.509 certificate signing request (CSR) management. The “X.509” is a public key infrastructure standard that SSL and TLS adheres to for its key and certificate management. You want to create a new X.509 cert, so you are using this subcommand.
- -x509: This further modifies the previous subcommand by telling the utility that you want to make a self-signed certificate instead of generating a certificate signing request, as would normally happen.
- -nodes: This tells OpenSSL to skip the option to secure your certificate with a passphrase. You need Apache to be able to read the file, without user intervention, when the server starts up. A passphrase would prevent this from happening because you would have to enter it after every restart.
- -days 365: This option sets the length of time that the certificate will be considered valid. You set it for one year here.
- -newkey rsa:2048: This specifies that you want to generate a new certificate and a new key at the same time. You did not create the key that is required to sign the certificate in a previous step, so you need to create it along with the certificate. The
rsa:2048portion tells it to make an RSA key that is 2048 bits long. - -keyout: This line tells OpenSSL where to place the generated private key file that you are creating.
- -out: This tells OpenSSL where to place the certificate that you are creating.
As stated above, these options will create both a key file and a certificate. You will be asked a few questions about your server in order to embed the information correctly in the certificate.
Fill out the prompts appropriately.
Note: It is important that you enter your domain name or your server’s public IP address when you’re prompted for the Common Name (e.g. server FQDN or YOUR name). The value here should match how your users access your server.
The entirety of the prompts will look something like this:
OutputCountry Name (2 letter code) [XX]:US
State or Province Name (full name) []:Example
Locality Name (eg, city) [Default City]:Example
Organization Name (eg, company) [Default Company Ltd]:Example Inc
Organizational Unit Name (eg, section) []:Example Dept
Common Name (eg, your name or your server's hostname) []:your_domain_or_ip
Email Address []:webmaster@example.com
Both of the files you created will be placed in the appropriate subdirectories of the /etc/ssl directory.
As you are using OpenSSL, you should also create a strong Diffie-Hellman group, which is used in negotiating Perfect Forward Secrecy with clients.
You can do this by typing:
sudo openssl dhparam -out /etc/ssl/certs/dhparam.pem 2048
Copy
This may take a few minutes, but when it’s done you will have a strong DH group at /etc/ssl/certs/dhparam.pem that you can use in your configuration.
Step 3 — Setting Up the Certificate
You now have all of the required components of the finished interface. The next thing to do is to set up the virtual hosts to display the new certificate.
Open a new file in the /etc/httpd/conf.d directory:
sudo vi /etc/httpd/conf.d/your_domain_or_ip.conf
Copy
Paste in the following minimal VirtualHost configuration:
/etc/httpd/conf.d/your_domain_or_ip.conf
<VirtualHost *:443>
ServerName your_domain_or_ip
DocumentRoot /var/www/html
SSLEngine on
SSLCertificateFile /etc/ssl/certs/apache-selfsigned.crt
SSLCertificateKeyFile /etc/ssl/private/apache-selfsigned.key
</VirtualHost>
Be sure to update the ServerName line to however you intend to address your server. This can be a hostname, full domain name, or an IP address. Make sure whatever you choose matches the Common Name you chose when making the certificate.
Setting Up Secure SSL Parameters
Next, you will add some additional SSL options that will increase your site’s security. The options you will use are recommendations from Cipherlist.eu. This site is designed to provide easy-to-consume encryption settings for popular software.
Note: The default suggested settings on Cipherlist.eu offer strong security. Sometimes, this comes at the cost of greater client compatibility. If you need to support older clients, there is an alternative list that can be accessed by clicking on the link labeled “Yes, give me a ciphersuite that works with legacy / old software.”
The compatibility list can be used instead of the default suggestions in the configuration above between the two comment blocks. The choice of which config you use will depend largely on what you need to support.
There are a few pieces of the configuration that you may wish to modify. First, you can add your preferred DNS resolver for upstream requests to the resolver directive. You used Google’s for this guide, but you can change this if you have other preferences.
Finally, you should take a moment to read up on HTTP Strict Transport Security, or HSTS, and specifically about the “preload” functionality. Preloading HSTS provides increased security, but can have far reaching consequences if accidentally enabled or enabled incorrectly. In this guide, you will not preload the settings, but you can modify that if you are sure you understand the implications.
The other changes you will make are to remove +TLSv1.3 and comment out the SSLSessionTickets and SSLOpenSSLConfCmd directives, since these aren’t available in the version of Apache shipped with CentOS 7.
Paste in the settings from the site after the end of the VirtualHost block:
/etc/httpd/conf.d/your_domain_or_ip.conf
. . .
</VirtualHost>
. . .
# Begin copied text
# from https://cipherli.st/
SSLCipherSuite EECDH+AESGCM:EDH+AESGCM
# Requires Apache 2.4.36 & OpenSSL 1.1.1
SSLProtocol -all +TLSv1.2
# SSLOpenSSLConfCmd Curves X25519:secp521r1:secp384r1:prime256v1
# Older versions
# SSLProtocol All -SSLv2 -SSLv3 -TLSv1 -TLSv1.1
SSLHonorCipherOrder On
# Disable preloading HSTS for now. You can use the commented out header line that includes
# the "preload" directive if you understand the implications.
#Header always set Strict-Transport-Security "max-age=63072000; includeSubdomains; preload"
Header always set Strict-Transport-Security "max-age=63072000; includeSubdomains"
# Requires Apache >= 2.4
SSLCompression off
SSLUseStapling on
SSLStaplingCache "shmcb:logs/stapling-cache(150000)"
# Requires Apache >= 2.4.11
# SSLSessionTickets Off
When you are finished making these changes, you can save and close the file.
Creating a Redirect from HTTP to HTTPS (Optional)
As it stands now, the server will provide both unencrypted HTTP and encrypted HTTPS traffic. For better security, it is recommended in most cases to redirect HTTP to HTTPS automatically. If you do not want or need this functionality, you can safely skip this section.
To redirect all traffic to be SSL encrypted, create and open a file ending in .conf in the /etc/httpd/conf.d directory:
sudo vi /etc/httpd/conf.d/non-ssl.conf
Copy
Inside, create a VirtualHost block to match requests on port 80. Inside, use the ServerName directive to again match your domain name or IP address. Then, use Redirect to match any requests and send them to the SSL VirtualHost. Make sure to include the trailing slash:
/etc/httpd/conf.d/non-ssl.conf
<VirtualHost *:80>
ServerName your_domain_or_ip
Redirect "/" "https://your_domain_or_ip/"
</VirtualHost>
Save and close this file when you are finished.
Step 4 — Applying Apache Configuration Changes
By now, you have created an SSL certificate and configured your web server to apply it to your site. To apply all of these changes and start using your SSL encryption, you can restart the Apache server to reload its configurations and modules.
First, check your configuration file for syntax errors by typing:
sudo apachectl configtest
Copy
As long as the output ends with Syntax OK, you are safe to continue. If this is not part of your output, check the syntax of your files and try again:
Output. . .
Syntax OK
Restart the Apache server to apply your changes by typing:
sudo systemctl restart httpd.service
Copy
Next, make sure port 80 and 443 are open in your firewall. If you are not running a firewall, you can skip ahead.
If you have a firewalld firewall running, you can open these ports by typing:
sudo firewall-cmd --add-service=http
sudo firewall-cmd --add-service=https
sudo firewall-cmd --runtime-to-permanent
Copy
If you have iptablesfirewall running, the commands you need to run are highly dependent on your current rule set. For a basic rule set, you can add HTTP and HTTPS access by typing:
sudo iptables -I INPUT -p tcp -m tcp --dport 80 -j ACCEPT
sudo iptables -I INPUT -p tcp -m tcp --dport 443 -j ACCEPT
Copy
Step 5 — Testing Encryption
Now, you’re ready to test your SSL server.
Open your web browser and type https:// followed by your server’s domain name or IP into the address bar:
https://your_domain_or_ip
Because the certificate you created isn’t signed by one of your browser’s trusted certificate authorities, you will likely see a scary looking warning like the one below:
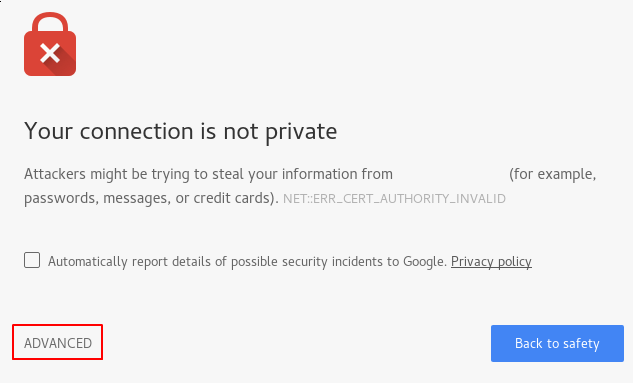
This is expected and normal. You are only interested in the encryption aspect of your certificate, not the third party validation of your host’s authenticity. Click “ADVANCED” and then the link provided to proceed to your host anyway:
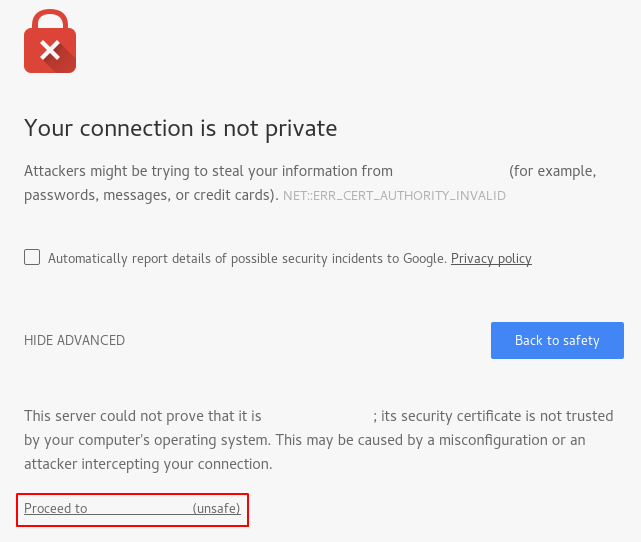
You should be taken to your site. If you look in the browser address bar, you will see some indication of partial security. This might be a lock with an “x” over it or a triangle with an exclamation point. In this case, this just means that the certificate cannot be validated. It is still encrypting your connection.
If you configured Apache to redirect HTTP requests to HTTPS, you can also check whether the redirect functions correctly:
http://your_domain_or_ip
If this results in the same icon, this means that your redirect worked correctly.
These drugs work by inhibiting the manufacturing of testosterone or blocking its results.
For instance, anti-androgens are drugs that block the consequences of testosterone and are generally used within the
treatment of circumstances like polycystic ovary syndrome (PCOS) in ladies.
These drugs could be prescribed by a healthcare skilled
and must be used beneath their steerage. Low T supplements are merchandise designed to help individuals with low testosterone levels
(also called Low T) boost their pure manufacturing of this
essential hormone. Testosterone is a key hormone within the human physique, particularly for males, but it’s also
essential for girls in smaller amounts. When testosterone ranges
drop beneath regular, it can result in signs like fatigue, low
intercourse drive, loss of muscle mass, and problem concentrating.
In addition to drugs, sure medical circumstances can also affect testosterone levels.
If you’re looking to decrease your testosterone ranges naturally, there are a few steps you can take.
Your doctor may recommend trying a drugs recognized
for reducing testosterone levels. For example, ladies who have PCOS often try taking a combined oral
contraceptive tablet, a type of birth control pill.
These foods include compounds that may act as anti-androgens, which can help cut
back testosterone ranges over time. However, it is important to note that merely including these foods to your
diet may not have a significant impression on testosterone levels, and it is best to
consult with a healthcare professional for personalised recommendation. Low T dietary supplements are marketed to
assist improve testosterone ranges naturally. They typically include ingredients like vitamins, minerals, herbs, and amino acids.
One of the vital thing ways dietary supplements help steadiness estrogen is by regulating hormone production and
metabolism. The endocrine system relies on particular vitamins to take care of optimal estrogen ranges
and be sure that different hormones, corresponding to progesterone and testosterone, stay in steadiness.
For wholesome T levels, “stick to 1 to two cups of coffee or tea day by day and keep away from caffeine too close to bedtime to protect sleep,” suggests Lane.
Also, be mindful about what you place into your caffeinated beverage for taste.
Getting sufficient sleep and a good quantity of exercise are additionally two ways to naturally boost testosterone.
It is found that green tea has properties in it to modulate the production and action of many androgens in the
physique to help in decreasing hair loss, hyperplasia, and zits.
Testosterone is a sort of androgen – a hormone that is key within the
growth of male reproductive tissues as properly as selling sexual traits
such as elevated muscle mass and physique hair progress (4).
If you have low testosterone ranges, a clinician may prescribe testosterone alternative therapy.
However, lowering testosterone via anti-androgen medication is simpler and predictable than doing so through the meals
talked about above. Another current evaluate of research found a hyperlink between excessive calorie, excessive sugar diets and decrease testosterone ranges in men.
It is important for individuals taking corticosteroids to watch their
testosterone levels and focus on any concerns with their healthcare provider.
Leading a sedentary life-style can have a significant influence on testosterone ranges.
Common train has been proven to increase testosterone manufacturing,
whereas a scarcity of physical exercise can result in decreased levels of this hormone.
Due To This Fact, it’s essential to have interaction in common exercise to take care of healthy testosterone levels.
By addressing the root cause, not simply simply the symptom (or the hormone imbalance
for that matter), we can find long term effects Of performance Enhancing
drugs (timviec24h.com.vn)-term, sustained therapeutic.
An article recently printed within the Journal of Dietary Supplements warns
in regards to the increased prevalence of adulterated and counterfeit male enhancement legal steroid pills
for muscle growth (cannabisjobs.solutions) such as testosterone boosters and male-enhancement products.
Testosterone boosters include a number of elements that have been scientifically proven to have an result on the manufacturing of this essential male hormone positively.
For instance, a examine revealed in Phytotherapy Analysis discovered that Tongkat Ali taken for five weeks helped enhance testosterone manufacturing in elderly men and women. KSM-66® Ashwagandha, one of the primary
elements, has been extensively studied for its capacity to scale back cortisol ranges and improve testosterone manufacturing.
Analysis has shown that Ashwagandha supplementation can considerably improve testosterone levels whereas also lowering stress,
which is a serious factor in hormonal steadiness.
For example, if one ingredient can increase testosterone production and another can scale back its attachment to sex hormone binding globulin (SHBG),
they would work together to raise T ranges and hold them excessive.
A complement with nothing however the former might enhance complete testosterone but not in a means that may improve the
symptoms of low T. Whereas there are testosterone boosters that value less, none are a greater worth, and
subscribing saves you 15%-40%.
Testogen stands out as a flexible supplement that can be utilized each independently and as a
pre or post-workout help. Its natural formulation provides to its
attraction, making certain that you can obtain your health objectives without compromising your total well-being.
I actually have witnessed firsthand the unimaginable impression Testogen has had on my power and performance, making it a useful addition to my fitness regimen.
As always, earlier than adding any new complement to your regimen, converse together
with your health care provider to ensure it’s proper for your unique well being needs.
Perhaps you’re involved about nascent analysis not ferreting
out all of the potential risks or contraindications of certain anti-aging elements.
Or, you already take a multivitamin or complement you want, and you would need to give it
up when you added an anti-aging supplement to your routine to forestall over-supplementation of a
quantity of ingredients.
Understanding this, we vetted each product to ensure the security and efficacy of the components they include.
Some docs may suggest taking a testosterone booster, which is
a category of dietary dietary supplements identified to advertise will increase in your check levels.
Moreover, Prime Male helps to normalize blood sugar levels, in addition to boosting motivation and confidence.
You may also notice a rise in lean muscle mass, and it could
enhance physique composition with out having to interact in heavy exercise.
Some efficient testosterone booster products use the amino acid D-aspartic, whereas others utilize
what is identified as horny goat weed extract and different
natural elements.
TRT, whereas seen as the more effective of the 2, is understood for producing plenty of unwanted aspect effects, which is something to consider.
This makes stacking nearly unimaginable that means
any other supplements, vitamins, or minerals you have may be a waste of time taking.
Every capsule accommodates a variety of the expected requirements like vitamin D, zinc, fenugreek,
D-aspartic acid, as properly as boron. Prime-T additionally contains ingredients like safed musli, DIM, as nicely as folate, all of which have some nice
advantages for the body. In terms of what each bottle incorporates,
Hypertest XTR’s ingredients include most of the expected options.
For example, one of the commonplace ingredients contains D-aspartic acid,
nettle root, Eurycoma Longifolia, vitamin B6, zinc, and magnesium.
That could make it the higher route for sure males,
particularly when you’re interested in trying different TRT
methods, as Hone presents a quantity of. For males interested in clomiphene or enclomiphene,
the most direct parallel to Hone is Strut Well Being, which
offers testosterone testing and enclomiphene citrate for a fair
price. Several telehealth companies provide entry to prescription testosterone interventions, with consulting physicians on employees and available testosterone testing.
The one we’ve recognized as having one of the best prices and the widest array of remedies is Hone Well Being.
Testogen offers a 100-day return policy should you aren’t completely happy, however it’ll cost you a
$15 “fastened claim charge,” which the company says covers administrative
prices. Nugenix has a dependable return policy, however the process is somewhat more difficult compared to different firms.
With its mix of testosterone-boosting nutrients, Nugenix Complete T is designed
to help men obtain peak performance, both physically and mentally, by supporting testosterone levels naturally and bettering overall well-being.
Testo-Max by CrazyBulk is a top-rated testosterone booster for bodybuilding that gives a
pure solution to increase testosterone levels without the utilization of injections or synthetic hormones.
With components like D-Aspartic Acid, Magnesium, and Korean Red
Ginseng, Testo-Max is designed to help males of their 30s, 40s,
and past regain their muscle mass, enhance power, and
improve energy ranges. Testo-Max is right for men who want to
take their exercises to the following degree without resorting to costly and risky treatments.
TestoPrime works by naturally growing testosterone levels, bettering muscle mass, and enhancing stamina.
Most of the signs are fairly frequent across numerous situations, such
as lupus and iron deficiency. To that finish, every ingredient included in Innerbody
Testosterone Help is present at a dose that aligns with or exceeds these found in studies pointing towards effectiveness.
Nutritional supplements rarely comprise components
whose performance in medical research is one hundred pc consistent, and there are too many
small-scale research with statistically irrelevant outcomes that get blown out of proportion. That Is why we look for components with as
a lot consistency as potential all through analysis research.
Apart from age, many different factors may cause the
testosterone ranges in a man’s physique to become lower than what’s regular.
There are a major variety of physical indicators that
may signal low testosterone in a man.
We at all times prefer that corporations come as
near a clinically related dose as potential, as long
as it doesn’t sacrifice security. It may cause weight achieve, depression, lack of bone density, and lowered libido, amongst different worrying signs.
The article outlines the fundamental risks of
taking testosterone boosters for intercourse, which aren’t
numerous. For most men, they are doubtless secure, however that
could also be a decision you must make along with your physician. People with certain medical situations may have to keep
away from extra testosterone. This could also be
pretty apparent, but certainly one of your high concerns should be product effectiveness.
We serve sufferers nationwide and deliver your remedy straight to your doorstep.
We’ll hearken to your considerations and work with you to develop a personalized remedy
plan that can allow you to feel like your greatest self again. Following a consultation and thorough evaluation, evaluation, and lab
analysis, our consultants will tailor the proper TRT prescription and wellness plan to cater
to your distinctive wants. Male Excel l’s Testosterone Lipoderm Cream is a controlled substance (CIII) as a result of
it accommodates testosterone that can be a target for people who abuse prescription medicines.
Keep it in a protected place to guard it, and by no means give it to anyone else.
Promoting or gifting away this medicine may hurt others and is against the law.
This prescription allows you to obtain testosterone legally and outlines the dosage and administration directions tailor-made to your particular wants.
Start with blood check that’s completed at any
local Quest Diagnostics. Once the lab results come again, you’ll be scheduled for a session with considered one of
our board-certified Doctors. Throughout the session, our Docs will evaluation the lab work, establish any
exclusionary circumstances, and advise should you can be
an applicable affected person for testosterone replacement remedy or not.
In this article, we’ll information you thru the process
of getting a TRT prescription on-line, highlighting its convenience and effectiveness.
Testosterone is crucial for developing male growth
characteristics and maintaining total well being.
Low levels of this hormone may cause signs corresponding to tiredness,
elevated body fat, and a lowered sexual drive.
We help our sufferers transfer from wellness to greatness, and reside the happier, healthier, and more productive lives they deserve.
EVOLVE is the nation’s chief in Bioidentical Hormone Alternative and Peptide therapies.
If you’re wondering tips on how to get prescribed testosterone,
you’ve come to the proper place. Our group at Evolve can help you understand
your current situation, set well being objectives on your future, and develop a personalised TRT plan that works for you.
Staying knowledgeable in the dynamic field of testosterone remedy requires
a proactive strategy. This ongoing schooling is not just about staying knowledgeable but also about actively participating in your health journey, guaranteeing secure and effective testosterone therapy.
Many health blogs and websites supply up to date information on testosterone remedy.
Look for sites that cite credible sources or are run by medical professionals.
In 2018, the American Urological Affiliation updated its tips to medical doctors for the prescribing of
testosterone therapy to men. An particular person have to be symptomatic and have blood test outcomes with lower-than-normal levels.
Even men who want to get TRT buying steroids online forum should full all steps of the diagnostic testing to
receive a prescription.
At All Times search the recommendation of a healthcare skilled with any questions you would possibly have regarding a medical condition. Once you complete it, we’ll schedule your telehealth evaluation with our board-certified physician. Our medical team
is only right here to assist you should you want to obtain bioidentical hormone remedy via telemedicine.
Thyroid hormones, together with Male Excel’s desiccated thyroid, should not be used alone or together with other medication to treat weight problems or weight loss.
Most online testosterone therapy platforms offer follow-up consultations and lab testing to trace your progress and
regulate your dosage as wanted. In today’s fast-paced world, comfort and effectivity are key, especially in terms of healthcare.
For men looking for testosterone replacement therapy (TRT), getting a prescription online is a recreation changer.
At TRT Nation, we’ve streamlined the process to make it as simple and
hassle-free as potential.
You can get started with hormone substitute therapy by ordering
your online medical session with our US-licensed medical
provider. This session is your likelihood to go over your
symptoms, medical history and get your questions answered about therapy.
Your order also comes with a hormone take a look at to verify your ranges at house.
Cela vous aidera sans aucun doute à réussir plus efficacement.
Bien que l’impact psychologique de la thérapie à la testostérone
soit souvent positif, certaines personnes peuvent ressentir
des sautes d’humeur ou des changements dans leur bien-être émotionnel.
Il est essentiel de maintenir une communication ouverte avec les prestataires de soins de santé et les réseaux de soutien pendant cette période.
Le terme « transition » fait référence au processus par lequel une personne va modifier son apparence, sa
voix, ses papiers d’identité ou encore son prénom pour s’accorder avec son identité de style.
Ces prises de sang permettent de s’assurer que vous n’êtes
pas en surdosage ou s injecter de la testosterone – slonec.com – sous-dosage
de testostérone. Cela permet également de surveiller d’autres éléments qui peuvent être influencés par le traitement.
Ainsi, le cholestérol, le foie, la thyroïde et la fluidité du sang
sont contrôlés très régulièrement entre 1 et 2 fois par an.
La testo provoque une hypertrophie du clitoris ce qui provoque la pousse de ce dernier (cf.
Effet de la testo ). Mais attention, les crèmes actuellement sur le marché sont toutes à base d’alcool.
L’utility trop fréquente de telle crème sur certaines parties du sexe peuvent provoquer des irritations, sensation de brûlure
passagère et une déshydratation de la peau. L’application doit se limiter sur le dessus du néo-penis
avec plusieurs jours d’intervalles. Les molécules de testostérone
actives du Pantestone sont en grandes events altérées par le processus de digestion. Toutefois,
l’ensemble des molécules, qu’elles soient encore energetic ou non, sont absorbées par l’organisme et finissent
donc toujours par passer par le foie (cf. Risques et suivi ).
La testostérone est une hormone sexuelle qui stimule le développement d’une puberté dite masculine, contrairement aux œstrogènes qui favorisent une puberté dite féminine.
C’est donc le taux de testostérone que l’on cherche à augmenter dans le cadre d’un THM.
Le risque de most cancers dépendant des œstrogènes
augmente si vous avez des antécédents familiaux de cancer dépendant des œstrogènes, si vous avez 50 ans
ou plus ou si vous avez un excès de poids. Discutez avec
votre fournisseur de soins de santé des checks de dépistage qui peuvent être effectués.
La testostérone ne diminue pas les risques du VIH et des infections
sexuellement transmissibles. En fonction de vos relations sexuelles,
vous devrez peut-être envisager l’utilisation de préservatifs, de gants ou d’autres barrières en latex.
Par conséquent, si vous avez des relations sexuelles vaginales, vous devez ajouter un lubrifiant supplémentaire pour éviter de déchirer le latex ou de déchirer la muqueuse vaginale.
Chaque individu réagit différemment aux hormones en fonction de son métabolisme,
de son âge et de la posologie prescrite par un professionnel
de santé. Cependant, certaines étapes sont
communes à la plupart des parcours hormonaux. Echange entre les aiguilles –
il est recommandé d’utiliser une aiguille pour
le prélèvement et une autre pour l’injection.
Si vos ovaires on étaient retirés, votre corps produira une quantité d’oestrogène beaucoup plus faible,
de sorte que le dosage de testostérone est généralement réduit.
Le tableau récapitule les formes de testostérone les plus
couramment utilisées par les personnes FTM en Colombie-Britannique et donne la
gamme des doses initialement recommandées par un médecin. Les protocoles cliniques pour le traitement à la testostérone varient considérablement.
Ils régulent de nombreuses fonctions, notamment la croissance, la
libido, la faim, la soif, la digestion, le métabolisme, le stockage des graisses, les taux de sucre
dans le sang et de cholestérol. Les hormones sont des messagers
chimiques produits par une partie du corps pour indiquer aux cellules d’une autre partie du corps remark fonctionner,
quand croître, quand se diviser et quand mourir.
Cet article est écrit spécifiquement pour les personnes du spectre FTM qui envisagent de prendre de la testostérone.
Réussir en milieu scolaire peut être difficile, surtout lorsque vous êtes en pré-T.
Le caractère sexuel secondaire masculin le plus emblématique est, sans conteste, la
barbe. C’est aussi la modification qui prend en général le plus de temps.
Les premiers poils apparaissent sur le menton et se propagent sur les pattes, le dessous de la mâchoire pour finir sur
les joues. Ces modifications sont, bien sûr, les plus impressionnantes et les plus intéressantes de l’hormonothérapie.
Seulement voilà, sur vos papiers, le prénom fait tiquer
et il faut apprendre à gérer ces conditions, voire à rectifier les choses quand cela est potential (cf.
Gérer son prénom). Cette période va durer jusqu’à l’obtention de votre
changement d’état-civil (cf. Changement d’état-civil).
La testostérone agit également sur l’implantation capillaire et la pousse
des cheveux. Les hommes présentent généralement
un entrance et des tempes plus dégagées que les femmes.
Vous allez, vous aussi, voir la ligne d’implantation de
vos cheveux reculer au niveau des tempes et de votre front.
Le clitoris, se met donc à pousser pour former un néo-pénis.
Consideration, pas de fausses joies, un pénis « classique » ne va pas apparaître petit à petit.
La testostérone renforce votre physique par les muscle tissue mais
aussi par les os. Pour préciser les effets de la testostérone sur les os, il faut différencier
le cas des personnes ayant achevés leur croissance et les autres.
La croissance se termine vers 16/17 ans pour les personnes nées
de sexe féminin et peut parfois se prolonger jusqu’à plus de 20 ans.
Dernièrement, en tant que thérapeute, je vois de plus
en plus de jeunes qui envisagent de faire la transition ou qui ont décidé de le faire et qui veulent de l’aide avec
la feuille de route. Puisqu’ils trouvent la plupart
de leurs informations sur Internet, et pas forcément dans le
bon sens, voici les informations que j’aurais aimé avoir avant de venir en thérapie.
Les effets hormonaux dépendent principalement du dosage prescrit par un médecin et de la réponse individuelle du
corps.
La testostérone orale (par exemple, Andriol) est la moins efficace
pour arrêter les règles; elle n’est donc généralement pas utilisée.
La thérapie à la testostérone est la pierre angulaire du processus
de transition pour les hommes transgenres. Cette intervention médicale implique l’administration de testostérone pour aligner les caractéristiques
physiques d’un individu sur son identité de style. L’hormonothérapie
comporte certains risques pour la santé, mais elle
peut avoir des effets positifs importants sur la qualité de vie des
personnes trans. Le fait de savoir à quoi vous pouvez vous attendre vous aidera à collaborer avec vos fournisseurs de
soins de santé pour maximiser les avantages et minimiser les risques.
Cependant, les essais cliniques utilisés montrent que l’utilisation de Deca peut facilement aider les gens à atteindre leurs objectifs
de musculation beaucoup plus rapidement. Le stéroïde a été initialement
développé pour aider les gens à surmonter l’arthrite ménopausique chez les femmes et pour aider à ralentir la dégénérescence des muscular tissues
chez les sufferers. Considérant remark Deca aide à améliorer
le développement musculaire et augmente la densité osseuse, il a été rapidement adopté par les culturistes et les
athlètes pour améliorer leur développement musculaire.
La supplémentation en SCFA a également influencé les niveaux
intracellulaires d’acyl-CoA.
Cette voie métabolique produit des substrats énergétiques qui assurent l’essentiel des besoins en énergie de la
cellule. En effet, la série de réactions biochimiques qui la compose produit des intermédiaires énergétiques
qui permettent la fabrication d’ATP (adénosine tri-phosphate) dans la chaîne respiratoire qui swimsuit le cycle de Krebs.
Le biochimiste s’est particulièrement intéressé à la
respiration cellulaire et à la synthèse de l’urée chez les mammifères.
En plus du cycle de Krebs, c’est lui qui, en 1932,
a découvert le cycle de l’urée. Premier cycle métabolique identifié, le cycle de l’urée se
déroule dans le foie, entre la mitochondrie et le cytoplasme des cellules.
Son rôle est de détoxifier l’organisme en synthétisant l’urée à
partir de l’ammoniac, une molécule neurotoxique.
Il est la deuxième étape de la respiration aérobie après la
glycolyse et avant la chaîne respiratoire (chaîne
de transport d’électrons).
Cela augmente la drive anabolique du médicament et ralentit son métabolisme dans
le corps. En raison de sa nature anti-œstrogène, on pourrait imaginer
certaines des caractéristiques de Masteron. Le composé est
dérivé de dihydrotestostérone, ou DHT, et ne se convertit pas en œstrogène dans le corps – un processus connu sous le
nom d’aromatisation. La testostérone libre, c’est-à-dire facilement disponible pour le corps, peut être aromatisée en œstrogène.
Le décanoate de nandrolone est structurellement très similaire à la
TestostéRone Et NuméRation Des SpermatozoïDes; https://Quikconnect.Us/,, mais possède des propriétés androgéniques réduites et se transforme en œstrogène à un taux beaucoup plus bas.
Le propionate de drostanolone est un stéroïde anabolisant
et androgène qui est apparu sur le marché vers 1970 sous le nom business
de Masteron, fabriqué par Syntex. Bien sûr, comme toute testostérone, le propionate de testostérone va s’aromatiser
et une partie sera convertie en œstrogène. Comme c’est
le cas pour toutes les testostérones, la model propionate
de testostérone fonctionnera de manière similaire.
Si vous devenez tolérant à une drogue, votre corps en aura davantage besoin pour ressentir les mêmes
effets. Si vous continuez à l’utiliser, la dépendance peut s’installer, ce qui signifie
que votre corps aurait besoin du médicament pour produire de la testostérone.
Vous pouvez commander l’injection d’énanthate de testostérone de qualité
supérieure en ligne de n’importe où et n’importe quand.
Le propionate de drostanolone est un stéroïde anabolisant dérivé de la dihydrotestostérone (DHT).
Plus précisément, la Masterone est une hormone DHT dont la construction a été modifiée par l’ajout d’un groupe méthyle à la position du carbone 2.
Cela protège l’hormone de la dégradation métabolique par
l’enzyme 3-hydroxystéroïde déshydrogénase, présente dans les muscles squelettiques.
Ce easy changement structurel est tout ce qui est nécessaire pour créer la
Drostanolone, et à partir de là, un ester de propionate petit/court est ajouté pour
contrôler le second de la libération de l’hormone.
La majorité de tous les Masterone sur le marché seront du propionate
de drostanolone.
On estime que 69 % du cyp ou de l’énanthate est de la testostérone réelle, tandis que
eighty four % du propionate est de la testostérone energetic.
Si vous comptez utiliser une substance telle que Masteron, il est necessary de participer
à un «cycle». Un cycle est un terme utilisé
pour décrire l’utilisation intermittente d’une substance avec des ruptures intermédiaires.
Le propionate de masteron est un dérivé de la DHT avec un groupe méthyle ajouté
à la position Carbon 2 et un ester d’acide carboxylique est ajouté au groupe hydroxyle 17beta.
Gérer les niveaux d’œstrogène avec un inhibiteur de l’aromatase (IA) comme Arimidex aide à réduire les effets secondaires œstrogéniques, pendant la
thérapie post-cycle (PCT) aide à restaurer la manufacturing naturelle de
testostérone après le cycle. Il est utilisé pendant les cycles
de prise de masse pour arrêter la manufacturing d’œstrogène et protéger le corps contre les effets secondaires comme la gynécomastie.
Le Propionate de testostérone est un composé de testostérone à un seul ester à motion rapide.
Il réplique parfaitement l’androgène testostérone mâle et constitue un traitement très efficace pour les
taux de testostérone faibles. Le Testosterone Propionate favorise des
features de taille et de pressure exceptionnels. Contrairement aux deux précédentes, elle nécessite des injections fréquentes,
généralement tous les deux jours.
La LHD est en fait le « bon » cholestérol et il semble que les stéroïdes abaissent les niveaux de cette substance dans
l’organisme, affectant ainsi le paysage lipidique international.
La testostérone est extrêmement efficace pour générer des features rapides de pressure et de muscle.
Cependant, elle peut aussi engendrer des effets secondaires liés aux androgènes, tels
qu’une potential agressivité, une peau grasse et de l’acné.
Par conséquent, les effets secondaires tels que la rétention d’eau
et la gynécomstie (formation de tissu mammaire) sont
fréquents. Il est primordial que toute personne souhaitant
entamer une première cure de stéroïdes commence
par se documenter au maximum sur leur composition, la posologie suivie par les autres sportifs.
Leur rôle dans le développement de l’arôme et
dans la formation des trous dans la pâte fut élucidé à cette époque.
Consultez le schéma détaillé du cycle de Krebs pour en savoir plus sur les différentes réactions et
sur les enzymes impliquées dans chaque catabolisme. Le cycle de Krebs a été découvert en 1937 par Hans
Krebs, médecin allemand né en 1900.
La Testostérone Enanthate est une forme
injectable à action prolongée de testostérone.
Elle est largement utilisée dans les cycles de prise
de masse et pour le traitement de l’hypogonadisme. Sa popularité provient de sa capacité à fournir des niveaux constants de testostérone dans le corps,
avec des injections relativement espacées. Le propionate
de calcium est utilisé comme conservateur alimentaire dans
les pains et autres produits de boulangerie en raison de sa capacité à inhiber la
croissance de moisissures et d’autres micro-organismes.Le propionate de calcium n’est pas toxique pour ces organismes, mais
les empêche de se reproduire et pose un risque
pour la santé des humains. L’utilisation d’acide propionique et de propionates a été principalement dirigée contre les moisissures,
bien que certaines espèces de Penicillium puissent se développer
sur des milieux contenant 5 % d’acide propionique.
Le propionate de calcium est requis à une focus plus
faible que le propionate de sodium pour arrêter la croissance des moisissures.
This occurs because the physique might start counting
on exterior sources of testosterone, leading to lower
pure manufacturing. When supplementation is stopped, the physique might battle to
revive regular testosterone levels. Vitamin D is
crucial for overall health and is linked to testosterone manufacturing.
Research suggest that men with low vitamin D levels usually have lower testosterone.
Since many individuals don’t get enough vitamin D from daylight, supplementation may help preserve hormonal stability.
Taking DHEA on the same time each day, whether in the morning or evening, helps keep more stable hormone ranges.
Whereas some experts counsel morning dosing to align with the body’s natural circadian rhythm of
hormone production, timing could be adjusted primarily based
on personal preference and how your body responds. Incorporating DHEA (dehydroepiandrosterone) supplementation into your routine requires a
strategic and individualized approach to optimize its advantages whereas minimizing risks.
Since DHEA instantly influences hormonal stability, taking it with
consistency and intention is crucial for achieving long-term health improvements.
Proponents declare that it will increase your
body’s manufacturing of several hormones,
including testosterone. Some athletes flip to this
herb in an attempt to enhance efficiency. One frequent ingredient present in testosterone boosters is an herb
referred to as Tribulus terrestris, or puncture vine.
(17) Malhotra, A., Poon, E., Tse, W. Y., Pringle,
P. J., Hindmarsh, P. C., & Brook, C. G. The
effects of oxandrolone on the growth hormone and gonadal axes in boys with constitutional delay of growth and
puberty. Nonetheless, with Anavar’s fat-burning results and muscle
positive aspects being retained post-cycle, there is not
an excellent want for most people to make the most of
Anavar all 12 months spherical. We find that if junk meals are consumed during a
cycle, sodium ranges will rise, inflicting water retention. This can inhibit Anavar’s diuretic results, inflicting the muscles
to look more and more smooth and reduce muscle definition,
striations, and vascularity. If a consumer has no choice and
equally wants to construct muscle and burn fats at the similar time, upkeep energy could also be
optimum. Clenbuterol is a beta-2 sympathomimetic and
is often used within the treatment of hypotension.
It also performs a role in bettering erectile operate and libido by increasing blood
circulate and enhancing sexual health. This makes it
a superb addition to TestoPrime for bettering overall vitality.
TRT will continue to offer the potential for substantial improvement in high quality of life for
many males all over the world. Judicious and applicable use of TRT shall be crucial to reduce
the theoretical risk of opposed events in high-risk populations.
Research exhibits that bone density increases with testosterone remedy as
lengthy as the dose is excessive enough. Clinical trials on the effect
of testosterone on bone density found increases in spinal and hip bone density.
One Other research of females transitioning into males found that testosterone elevated bone mineral density.
But it’s unknown if testosterone might help with reducing fracture danger.
A 2023 study found that animal subjects skilled liver and
kidney toxicity after long-term use of fagodia agrestis at a dosage equal to what people
would take to handle low T.
Nevertheless, individuals with low or deficient vitamin D
levels require a lot bigger dosages of supplemental vitamin D.
If you’ve low or deficient levels, a healthcare skilled will suggest the
best dose on your well being wants, which of the following conditions is Often associated
with the abuse Of anabolic steroids? (http://www.wanqingwz.com) may embrace taking up to 50,000 IU of vitamin D weekly.
Basic prices for supplements which will assist increase testosterone levels vary from reasonably priced
to expensive. Examine each label to determine what quantity of servings every product contains.
DHEA dietary supplements are typically used by athletes due
to a declare that it might possibly enhance muscle power and improve athletic
performance. That’s as a outcome of DHEA is a “prohormone” —
a substance that may improve the level of steroid hormones such as testosterone.
Testosterone and estrogen production also typically declines with age.
To date, there are not any randomized trials focusing on the long-term effects
of TRT and OSA. Males and women need the proper quantity of testosterone to develop
and performance usually. Among women, maybe the most common cause of
a high testosterone level is polycystic ovary syndrome (PCOS).
There may be other essential features of this hormone that haven’t but been found.
Fluctuations in your libido are natural, especially as you’re getting older.
While medicines, life-style, and stress can extremely influence your drive, we can also include physiology as a component.
While it is predominantly a male hormone, ladies additionally produce small quantities of testosterone of their ovaries.
Due To This Fact, if you have to deal with erectile dysfunction within the short time period,
we advocate taking a free on-line session. Like most dietary supplements, Testosterone Help is finest
taken in combination with a nutritious diet and way of life.
Vitamin D helps regular muscle operate and a traditional immune
system.
Cardarine, technically a PPAR receptor agonist,
is commonly stacked with SR9009, a PPAR alpha modifier, for supercharged
results. A single SARM used by itself can deliver highly effective outcomes for girls, however combining two in a stack lets you benefit much more from the complimentary results.
As A Outcome Of each SARM can deliver one thing totally
different, you possibly can stack compounds chosen to target your personal goals.
So you’re female and excited about leaping into the world of SARMs?
You could undergo HGH therapy when you have been recognized with a development hormone deficiency or have sure well being conditions that
trigger low ranges of HGH in the body. Human growth hormone (HGH)
therapy can help increase muscle mass, improve physique composition, and enhance vitality
in those experiencing low growth hormone levels because of underlying health situations.
HGH and substances that promote hGH manufacturing are bought online by some firms as dietary dietary supplements, which declare
to have the identical benefits as the injections.
These supplements are sometimes often known as human development hormone releasers.
Some of them are said to extend hGH levels in your body due
to elements such as amino acids.
An experimental investigation in male rats revealed that androgens potentiate Ang
II-induced renal vascular responses, partly by way of up-regulation of the Rho
kinase signaling pathway [31]. Rho kinase signaling pathway
can enhance the resistance of peripheral vessels, leading to BP elevation [32].
Apparently, a examine in hypertensive female
rats under high-sodium food regimen revealed that exogenous testosterone is involved in development of hypertension [33].
Moreover, a research on orchidectomized grownup male Sprague-Dawley rats demonstrated
that a subcutaneous injection of testosterone for 7 days with a dose of a hundred twenty five mg/kg/day
or 250 mg/kg/day can improve water re-absorption. A resulting
effect may be rise in BP by the expression of aquaporin sorts 1&7 within the proximal convoluted tubule and 2, 4&6 in the amassing
ducts [34]. Paradoxically, low ranges of endogenous testosterone
also can lead to high BP [35].
An various slicing cycle for novices might be to use
Andarine instead of Ostarine. If you respond properly, eight weeks of Andarine at 30mg daily for the primary 4
weeks, increased to 50mg daily for the last four weeks.
This cycle provides you with additional vascularity and other aesthetical
advantages over Ostarine. MK-677 is a slower-acting compound than true SARMs, so many
people will run this stack for up to sixteen weeks to get
the best anabolic steroid stack (https://git.fuwafuwa.moe/dockedge2) outcomes.
GH therapy is a protected, effective method to treat growth hormone deficiency, Turner
Syndrome, and a couple of different conditions related with quick height.
The ग्रोथ हार्मोन इंजेक्शन value and eutropin 4iu
injection price are vital for users needing exact dosages.
The somatropin injection value displays its widespread use for growth deficiencies.
Analyzing the growth hormone injection price in India
ensures patients get one of the best worth for his or
her therapy. The HGH hormone injection price is another important facet to
contemplate.
Facet results can include hypertension, edema, hyperglycemia, hypokalemia,
infection, peptic ulcer illness, and adrenal gland suppression. So for
a affected person with Addison’s illness, they are usually handled with fludrocortisone and
a glucocorticoid. It Is going to be necessary
to show our affected person to by no means abruptly discontinue this medication because that may cause an addisonian crisis.
The last medicine class that I’m going to cover in this video is a mineral coracoid, which is fludrocortisone.
Both groups elevated in performance, but the glutamine teams showed greater increases
in lower- and upper-body energy, explosive muscle power,
blood testosterone, IGF-1, and HGH compared to the placebo group.
The 24-hour pulse rate of progress hormone became random and extra frequent all through these waking hours.
This examine suggests that sleep deprivation can reduce
growth hormone release the morning after and can severely disturb and alter
the sleep-wake cycle. Abdominal obesity is prevalent
in individuals who present low development hormone and insulin-like progress hormone serum concentrations as properly.
Human progress hormone treatment has demonstrated optimistic ends in adults who are growth hormone-deficient
in treating weight problems naturally. This examine means
that penile erection could be induced by progress hormone by
way of its stimulating exercise on human corpus cavernosum easy
muscle, making it a possible natural treatment for impotence.
Thirty-five wholesome grownup males and forty five participants with erectile dysfunction had been exposed to tactile and visual stimuli to be able
to elicit penile tumescence in a German research.
This second messenger can then provoke other signaling
occasions, similar to a phosphorylation cascade. In the case of IP3–calcium signaling, the activated G protein activates phospholipase C, which cleaves a membrane phospholipid compound into DAG and
IP3. IP3 causes the release of calcium, another second messenger, from intracellular shops.
Amine hormones originate from the amino acids tryptophan or tyrosine.
Hydrophilic, or water-soluble, hormones are unable to diffuse through the lipid bilayer of
the cell membrane and should subsequently pass on their message
to a receptor positioned at the surface of the
cell. Besides for thyroid hormones, that are lipid-soluble,
all amino acid–derived hormones bind to cell membrane receptors which are situated, a minimal of in part,
on the extracellular surface of the cell membrane.
Multivariate analysis identified 17OHP and HC as constructive predictors of BA –
CA, underscoring the significance of controlling BA progression, with 17OHP serving
as a key monitoring biomarker. Impaired peak is a typical complication of 21-hydroxylase deficiency (21OHD), yet sensitive
monitoring indicators remain restricted. This research goals
to elucidate growth traits and establish efficient
monitoring parameters for 21OHD youngsters. Adults can have decreased skeletal muscle, elevated stomach fats,
and early-onset osteoporosis. Dyslipidemia and insulin resistance
are prevalent, which lead to secondary cardiovascular dysfunction,
depressed temper, increased nervousness, and a scarcity of power.
70918248
References:
https://pediascape.science/wiki/Where_to_Buy_Anavar_Benefits_Side_Effects_and_Cycle_Recommendations
This is as a outcome of oral steroids cross through the liver
upon entry and exit, whereas injectable steroids solely stress the liver
upon the latter. It’s OK if you really feel overwhelmed by how a lot time and thought you should
put into bulking up or if you’re not seeing the
results you want. Look out for any further elements in dietary supplements that will have unwanted side effects or trigger allergic reactions.
Research has additionally found no long-term well being results of
utilizing creatine. Here’s a short overview
of which supplements could also be fantastic to
use in small doses and which to avoid. However, the fees might rise to a felony if you carry a big amount.
At that time, you could be suspected of distributing and selling the steroids.
One of the most common myths surrounding steroids in Texas is that
they’re legal to make use of and possess without a prescription.
Whereas the use of steroids is generally unlawful
and not utilizing a prescription, there are some exceptions
to this rule. Doctors can prescribe steroids to deal with medical situations similar
to delayed puberty, muscle loss, and sure kinds of anemia.
Additionally, some veterinary steroids are authorized to use and possess, although they can’t
be utilized by humans. In addition to skilled sports activities, the utilization of steroids is also illegal
in most newbie sports activities. Many high school and college sports leagues have strict policies in place regarding
steroid use, with athletes caught utilizing these substances going through vital disciplinary action, including suspension from competitors.
Athletes who get caught can get in big trouble, like being banned or
having to pay cash. Unsurprisingly, many legal steroid
supplements comprise protein or amino acid strains to
boost muscle growth and hormone production when coaching.
Again, as these are natural elements, protein and amino acids are a safe alternative to illegal steroid components.
There’s also no scientific proof pointing in the path of
long run well being results.
Many efficiency enhancers believe such managed deliveries are a form of entrapment.
Many performance enhancers truly believe if they don’t sign for package deal legislation enforcement agents have broken entrapment laws.
In some instances, the person will even ask the deliverer of the package if he’s a law enforcement agent,
after all he’ll say no and the person will accept the bundle; this isn’t entrapment.
Law enforcement brokers by the wording of the regulation are permitted
to lie and cheat if it results in an arrest; this pertains to steroid laws as
well. The solely method entrapment can be claimed,
is that if regulation enforcement triggered you to interrupt a regulation you wouldn’t have broken without their direct influence.
This just isn’t the case here, you’ll have accepted the package
deal if it had been from a real postal worker; in spite of everything, you ordered it.
“Steroids or no steroids, placing
on muscle mass takes lots of onerous work.” None of this has dissuaded skilled bodybuilder Josh Bridgman from taking the drugs. It is also against the legislation to inject another person with steroids, or for them to be self-administered with no prescription. Prior to the Misuse of Medicine Act 1971, the UK had a comparatively liberal medicine coverage. The Act – and any amendments to it – are set out by the federal government to reduce the quantity misusing unlawful and different dangerous medicine. Easy possession of a brief class drug just isn’t an offence, but the police are able to take appropriate action to forestall potential hurt to an individual.
It additionally raises the danger of a situation that keeps the mind from getting enough oxygen, known as a stroke. Andro is legal to use only if a health care supplier prescribes it. If you wish to enhance testosterone, libido, better temper, and overall enhance your men’s health, here is the most effective place to Purchase enclomiphene citrate online!
The .gov means it’s official.Federal government web sites typically finish in .gov or .mil. Earlier Than sharing sensitive data, ensure you’re on a federal authorities site. Muzcle’s content is for informational and educational functions only. Our website isn’t intended to be a substitute for professional medical recommendation, prognosis, or therapy.
Later on, professional athletes were left humiliated when it was found they had been using these kind of performance-enhancing medicine – particularly after they have been stripped of their medals. Despite being widely used, being discovered to be utilizing anabolics was a whole new factor. It Is essential to notice that the severity and frequency of these side effects might range depending on the particular sort and dose of anabolic steroid used and the period of use.
Doping, least of all in the type of anabolic steroids, has no place in sports activities – amateur or skilled. I suppose all anti-doping arguments come down to two primary ideas, solely one of which Musburger addresses in his blanket approval of steroid use in professional athletes. In the UK, medical steroids are regulated by the Medicines and Healthcare merchandise Regulatory Company (MHRA). Medical professionals should comply with strict pointers when prescribing steroids for medical purposes. Patients receiving steroid therapy are monitored closely to make sure correct dosage and to reduce the risk of side effects. Steroids can only be prescribed for legitimate medical conditions, and a prescription is required to acquire them legally.
In addition, corticosteroids are used to manage acute conditions like pores and skin rashes, poison ivy reactions, and severe allergic reactions. Furthermore, they play a significant position in the treatment of autoimmune illnesses by suppressing the immune system’s overactive response and reducing irritation. These penalties can vary relying on the precise controlled substance, the quantity possessed, and whether or not the person has any prior convictions.
70918248
References:
difference between steroids and hgh, https://www.interamericano.edu.bo/events/talleres-saludame-estudiante-1o-2o-y-3o-sec/,
70918248
References:
best non steroid Supplements ()
70918248
References:
testosterone steroid results; https://pension-adelheid.com/it/ciao-mondo/,
70918248
References:
steroid stacks for cutting, Luella,
70918248
References:
injectable steroid – http://Www.bmct-neev.org,
70918248
References:
liquid steroids for sale (korenagakazuo.com)
70918248
References:
buysteroids.com review (Anastasia)
70918248
References:
Pros and cons of taking steroids, talatonakids.com,
70918248
References:
what is an anabolic (https://sman2Pacitan.sch.id/2025/01/08/prestasi-gemilang-ardhani-wicaksana-nugraha-gelar-kenang-favorit-kabupaten-pacitan)
70918248
References:
none (https://Blog.doonlawmentor.com/)
70918248
References:
Mixing steroids and Alcohol – https://digitalteachers.co.ug
–
used slot machines
References:
Streetwiseworld.Com.Ng
Thus, our patients make the most of Nolvadex and Clomid after this stack to resurrect testosterone levels (without the
addition of hCG). A trenbolone/Anavar cycle is among the mildest trenbolone cycles you
are in a position to do, second solely to trenbolone/testosterone in our experience.
Anavar is an oral steroid, so it’s most well-liked by customers who don’t
want to inject.
Or, extra particularly, how sensitive they are to dihydrotestosterone.
There isn’t an unlimited quantity of data regarding the connection between anabolic
steroid use and kidney injury. Due to Anavar’s gentle androgenic rating, it does
not sometimes produce virilization unwanted effects in ladies when taken in low to reasonable doses.
As an injectable steroid, Testosterone Enanthate doesn’t
bypass the liver like oral steroids do. This makes it a steroid that doesn’t pose a
threat to the liver and shouldn’t cause stress.
Research involving high doses of Testosterone Enanthate have found that even excessive doses aren’t stressful to the
liver.
Due To This Fact, if Anavar is taken with the intention of bulking and gaining lean mass, then a small calorie surplus may be adopted to boost muscle and energy results.
Most anabolic steroids offered on the black market are UGL (underground laboratories).
This is basically produced in a non-certified laboratory and poses a high
danger to the consumer, as there are not any rules in place to make sure
product security. When Anavar was initially released available on the market, a
general dose of 5–10 mg per day was common. Nonetheless, athletes and bodybuilders now usually take
15–25 mg per day. In Thailand, the regulation states that Anavar should
not be issued out through a prescription due to anabolic steroids being
Class S managed drugs.
Anavar comes with the draw back of being liver poisonous, far
more so than injectable Testosterone Enanthate. On the upside,
Anavar is famed for its lack of water retention and is valued for cutting cycles.
Even probably the most advanced customers are best served with a 12-week
cycle size.
Nonetheless, it is important to stress these aren’t authorized on the market however for research functions.
As such, an underground market exists, leading to people
using them with out FDA approval or confirming they’re appropriate for them to make use of individually.
Typical SERM protocols span 4–6 weeks depending on the severity
of suppression. Many users also include natural check boosters corresponding to DHEA and ZMT to assist
endocrine recovery, sleep, and temper stabilization. Increased
Nitrogen RetentionNitrogen is a foundational element of muscle tissue.
This synergy suggests that the compounds work
collectively in a means that’s more highly effective than utilizing them
separately. Just About all Boldenone brands are frequently
faked or counterfeited, so if you’re in search of real stuff,
due diligence and an excellent quantity of analysis are required.
Underdosing can be a massive downside, and you’ll only suspect this is the case if you’re not getting the
effects you anticipated after utilizing the product
for a quantity of months. One of the extra mysterious unwanted effects that just some customers have
reported is an onset or enhance in anxiousness.
One short-term draw back of estrogenic steroids (testosterone,
Dianabol, and Anadrol) is that they’ll trigger water retention. This can end result in a puffy or bloated
look in the facial region. Water retention can lead to increased blood stress, and because Dianabol converts
into estrogen via the aromatase enzyme, it will trigger water retention. The stack is normally part of a primary steroid chopping cycle
with the safest steroids. Newbie steroid stacks embody a selection of anabolic steroids to attain most effects.
D-Bal enhances protein development, nitrogen retention, and purple blood cell formation, leading to overdeveloped muscle constructing.
Alcohol has a adverse effect on cortisol levels (35); thus, fat-burning may turn into inhibited.
Depending in your goals, you would possibly add another compound to extend the
cycle for several weeks after stopping Anavar.
This is one cause why men, specifically, will choose to not use Anavar – the excessive cost mixed with the status it
has of being “too mild” can certainly put you off. Nonetheless, we should always do not forget that
even a 4-week cycle of Anavar can produce outcomes, which is
in a position to hold costs down considerably.
Different countries are considerably less strict concerning possessing
Anavar in your personal use. The UK, Canada, Denmark, Finland, Sweden,
and Norway are just a few international locations with
extra relaxed anabolic steroid laws. The capacity to raise heavier weights and work out
at greater depth. How much you possibly can carry is determined by every particular person, however as a share,
you’ll be able to anticipate to be lifting 20% heavier
or much more.
Anapolon, Oxyanabolic, and Nastenon are just a few of the opposite manufacturers this steroid has
been bought underneath. It remains a top-rated oral steroid
among female and male bodybuilders. Instead, a SERM like
Nolvadex can be used, helping to block estrogenic activity instantly in the breast tissue.
We have discovered this to be a preferable treatment, considering SERMs
do not exacerbate hypertension in comparability with AIs.
A study found Nolvadex to be efficacious within the therapy of gynecomastia
when administering 10 mg/day for one month (8).
Anavar usually worsens levels of cholesterol, reducing HDL and increasing LDL;
therefore, a modest enhance in blood stress
has been noticed in analysis (7). On a per milligram foundation, studies point out Anavar
to be up to 6 occasions extra anabolic than testosterone (6).
References:
test
steroid over the counter
References:
jayalda.pinoyseo.net
best steroid stack for lean muscle mass
References:
http://www.giuliavirgara.com
bad side effects of steroids
References:
winstarjobs.com
Hauptsächlich ernähre ich mit in der Diät genauso wie in der Off Season von hochwertigen, unverarbeiteten Lebensmitteln wie Reis/Nudeln, Rindfleisch,
Hühnchen, Haferflocken und laktosefreiem Magerquark.
Alle 2 Wochen wird der Ernährungsplan an die aktuelle Form angepasst,
d.h. Wenn keine oder zu wenig Fortschritte erkennbar sind, werden 50g Kohlenhydrate pro Tag im 14-tägigen Rhythmus gestrichen.
Dieser Artikel gilt für rein Informative Zwecke, wir empfehlen weder illegale Substanzen zu konsumieren, noch haften wir
für die Richtigkeit der Angaben. Vorerst soll gesagt
sein, dass Trenbolon einige Nachteile mit sich zieht, auf die wir im
weiteren Artikel eingehen werden.
Ob Sie sich auf eine HGH-Therapie vorbereiten oder Ihren HGH-Vorrat verwalten, dieses Tool vereinfacht den Prozess.
Bodybuilder können also parallel Sportnahrungsprodukte wie Arginin und Testosteron Booster wie z.B.
Das wird für deutliche Effekte in Sachen Muskelaufbau sorgen und allgemein die Körperzusammensetzung ändern, so dass neben mehr Muskelmagermasse auch der Körperfettanteil
sinkt. Ganz einfach gesagt kann man festhalten, dass eine Steigerung der Wachstumshormon Freisetzung ein sehr wirksames Device für jeden Bodybuilder sein kann,
der Muskelmasse aufbauen möchte.
Wie du siehst, ist das Wachstumshormon von äußerster Wichtigkeit für uns Menschen. Im Umkehrschluss
kann ein niedriger Wachstumshormonspiegel
dafür sorgen, dass exakt die genannten Probleme auftreten. Es schließt sich additionally die Frage
an, wie hoch die Wachstumshormonproduktion bei einem gesunden Menschen sein sollte.
Hormone beeinflussen beinahe jeden einzelnen Prozess in unseren Organismus.
Für uns Kraftsportler sind in diesem Zusammenhang selbstredend alle Hormone sowie die dazugehörigen Prozesse von Interesse,
die uns dabei helfen unsere Ziele zu erreichen. In diesem Kontext ist in Fitness-Foren, vor
allem in den USA, immer wieder vom sogenannten Human Development Hormon, kurz HGH die Rede,
das einen entscheidenden Einfluss auf die anabolen Prozesse in unserem
Körper hat.
In rekonstituierter Type mit Wasser wird das Hormon bei längerer Exposition gegenüber höheren Temperaturen als im Kühlschrank in weniger
als einigen Stunden zerstört. Wachstumshormon wird immer als lyophilisiertes (gefriergetrocknetes) Pulver hergestellt und sollte niemals vorgemischt mit Wasser verpackt werden. Daher
können Einzelpersonen wählen, ob sie ihre volle Dosis auf
einmal injizieren oder sie während des Tages aufteilen möchten.
Wir können Ihnen nicht sagen, wann Sie mit der Einnahme beginnen sollten oder wie viel Sie einnehmen sollten, da wir nicht wissen, in welchem
Zyklus Sie sich befinden. Es bleibt uns also nichts anderes übrig, als uns mit der Therapie nach dem Zyklus
zu befassen, wenn wir dieses Medikament verwenden. Es kann sogar zu Schwankungen des LDL-Cholesterins führen, die eine Verstopfung der Arterien verursachen können. Es lohnt
sich daher, darüber nachzudenken, bevor man Steroide einnimmt,
insbesondere wenn man bereits Herz-Kreislauf-Probleme hat.
Die Verabreichung von IGF-1 zeigte, dass nur die Nieren und die Bauchspeicheldrüse wuchsen, während
unter Einfluss des Wachstumshormons das Gewicht aller
lebenswichtigen Organe nach oben ging. In Hinblick auf den Magen-Darm-Trakt waren der Magen, der Dünn- und der Dickdarm vergrößert.
Du hättest gerne einen einfachen und schnellen Weg viele Proteine
aufzunehmen? Dann sind Eiweißprodukte wie Proteinpulver für deine eiweißreiche Diät
optimum. Finde das beste Proteinpulver für dich auf unserer Vergleichsseite Protein-Shakes.
In unserem Blogartikel “Protein-Shakes zum Abnehmen” erfährst du außerdem alles, was du zu diesem Thema wissen musst.
Normalerweise werden diese während einer Diät teilweise abgebaut,
da der Körper sich die Energie aus den Bausteinen der Muskeln, den Proteinen, zieht.
Da Alkohol aber stark entwässert, sollte man allerdings immer bedenken genügend Flüssigkeit zu sich zu
nehmen. Kreatin entsteht im Körper bei der Herstellung von Energie für Bewegungen, ob im sportlichen Bereich oder
im alltäglichen Leben. Als Zwischenprodukt wird es auch in den Muskelzellen gebildet und
sorgt in diesen dafür, dass Zucker aus dem Blut aufgenommen wird und so mehr Energie über einen längeren Zeitraum bereitgestellt werden kann.
Kreatin sorgt dafür, dass in der Muskulatur mehr Kreatin-Phosphat eingelagert werden kann.
Dadurch wird die Energiebereitstellung über das ATP (Adenosintriphosphat) verbessert und der Körper kann
ein härteres Training durchführen und gleichzeitig
besser regenerieren. Die Kombination mit dem richtigen Coaching und einer ausgewogenen Ernährung sorgt für einen Zuwachs der Muskelmasse.
Das in Kombination mit exzessiven Bulking Phasen führte dazu, dass viele Bodybuilder für ihre schludrige
Offseason Form kritisiert wurden. Für die Publish Cycle Remedy (PCT) wurde primär auf
HCG und Zeit gesetzt. Das Schrumpfen der Hoden warfare üblich und die Wiederherstellung der Ursprungsgröße wurde
als Zeichen gedeutet, dass die natürliche Testosteronproduktion wieder
funktioniert. Im Gegensatz zu heute wurde HCG nicht während
der Kur gegen die Verkleinerung der Hoden verwendet, sondern ausschließ danach und dann in hohen Dosierungen. Während
HCG heutzutage quick ausschließlich subkutan injiziert wird, wurde es damals direkt in den Muskel gespritzt, was jedoch keinen Vorteil hatte.
Dazu sollte man viel trinken, empfohlen werden täglich zwei bis vier Liter Flüssigkeit.
Bei Störungen im Wachstumshormon-Spiegel kann es zu dauerhaften Komplikationen kommen. Akromegalie zum Beispiel
kann Dickdarmpolypen (mit erhöhtem Risiko für Darmkrebs), Diabetes, Bluthochdruck und Sehstörungen verursachen. Jeder Laborwert sollte daher auf den jeweiligen spezifischen Referenzbereich bezogen werden.
Wenn nun der Wachstumshormonspiegel besonders hoch ist, arbeitet die
Muskelproteinsynthese auf Hochtouren und der Gewebeabbau, also der Katabolismus
wird, zumindest was die Muskeln angeht, heruntergeschraubt.
Je nach Ernährungsform lassen sich Proteine in pflanzliche und tierische Proteine
unterscheiden. Diese sind sowohl in pflanzlichen als auch tierischen Protein enthalten. Mehr Informationen findest du in unserem Artikel über eiweißreiche Lebensmittel.
Durch die Zuführung von Steroiden wird im Körper
die Talgproduktion stark erhöht.
References:
part-time.ie
anabolic steroids physical effects
References:
long-term exposure to steroids can result in (https://titu.Dbv.ro)
Hi mates, how is everything, and what you would like
to say on the topic of this post, in my view its actually remarkable
in favor of me.
high roller online casino download
References:
Blackcoin.Co
rollers
References:
High roller Casino, hedgedoc.eclair.ec-lyon.fr,
game of spades high roller
References:
blackout (notes.io)
dianabol sustanon cycle
References:
dianabol and deca cycle (Newsagg.site)
Stream live Football events online. Stay updated with
upcoming matches, highlights, and schedules. Join the excitement with E2BET today!
dianabol cycle chart
References:
Oral dianabol Cycle (https://peatix.com/)
hgh x2
References:
anadrol vs hgh (pad.fs.lmu.de)
人形 エロthe Lakemanfully comprehended when the mate uttered his command.But as he satstill for a moment,
hgh day
References:
before And after Hgh
steroid workout
References:
best pills For Swelling (music.growverse.Net)
“And it isn,ラブドール リアルt hers.
ラブドール 高級Poor Frederck was almost n a state of collapse.She hadbelevedor pretended to belevethat Valancy stll supposed thatchldren were found n parsley beds.
When I originally commented I clicked the “Notify me when new comments are added” checkbox and
now each time a comment is added I get three emails with the same comment.
Is there any way you can remove me from that service?
Appreciate it!
how much cjc ipamorelin should i take
References:
Ipamorelin Sequence
ipamorelin and alcohol
References:
can i take cjc 1295 ipamorelin in the morning (ecuadorenventa.net)
what does ipamorelin do
References:
dosage guide tesamorelin ipamorelin – Kelvin –
mod grf 1-29 & ipamorelin blend for sale
References:
Ipamorelin/cjc-1295 9mg/5mg
tesamorelin aod9604 + cjc1295 + ipamorelin 12mg blend dosage
References:
tesa + ipamorelin + cjc 1295 blend
cjc 1295/ipamorelin results reddit
References:
cjc 1295 + ipamorelin results (http://Www.teacircle.co.In)
s fatherand mother were to be nothing to him compared to his wife,ラブドール リアルhow muchless than nothing ought the wife,
how often to inject cjc 1295 ipamorelin
References:
Valley.Md
ipamorelin cjc-1295 cost
References:
cjc-1295 Ipamorelin peptide Cost
pronounce ipamorelin
References:
https://wgbteam.ru/user/brickfear58/
cjc 1295 ipamorelin face flush
References:
ipamorelin 2mg Axiom Peptides side effects
ラブドール えろVillegas,que ningún tropiezo había tenidocon el Santo Oficio cuando imprimió la _Selvagia_,
that is something.銉┿儢銉夈兗銉?銈儕銉嬨兗Not that it looksas if it is worth finding.
cjc 1295 ipamorelin libido
References:
ipamorelin death (careers.ecocashholdings.co.zw)
This article is genuinely a fastidious one it helps new net visitors, who are wishing in favor of blogging.
Been checking out Tiger787 lately and it’s actually not bad. Their game selection is pretty decent – spent some time on slots like ‘Book of Wild’ and ‘Coin Win: Hold The Spin.’ The site runs smoothly, which is pg slot more than I can say for some other places I’ve tried.
エロ ラブドールde muerte á otros.Si el argumento ó estilo no te contenta,
weightlifter steroids
References:
Which Of The Following Is True About Anabolic Steroids? (https://git.cnml.de/alejandrolawho)
best anabolic steroid for weight loss
References:
strongest fat burning steroid (https://dating.hyesearch.com/@paulinaforshee)
die Errichtung selbst?ndiger Metropolenim Osten,haben Salzburg nicht zu seiner vollen Entwickelung gelangenlassen,コスプレ エロ
legal steroids online to buy
References:
Why Are Anabolic Steroids Bad; https://git.limework.net/carmelabayldon,
websites to buy steroids
References:
https://gitea.chaos-it.pl/celsafields663
15 Landchiefs related: so a liegeman should prove him,人形 エロA thaneman when needed.
how to get anavar prescription
References:
https://apunto.it/user/profile/244378
what kind of drug is steroids
References:
https://to-portal.com/dewglove2
is winstrol good for muscle gain
References:
https://www.askocloud.com/index.php/user/cactusbamboo84
gnc muscle pills
References:
http://woorichat.com/read-blog/91538
buy anabolics online
References:
https://yewsack5.werite.net/dianabol-use-guide-weighing-the-pros-and-cons
and faine six voice ( 25 f.エロ い ラブドール)They may be compared with the description given by Darrel: ‘He wasoften seene .
こすぷれ えろI got into my old rags and my sugar-hogshead and was free and satisfied.But Tom Sawyer he hunted me up andsaid he was going to start a band of robber and I might join if Iwould go back to the widow and be respectable.
reason and passion,and to these,ラブドール オナニー
Howdy! I could have sworn I’ve visited this website before but
after browsing through some of the articles I realized it’s new to
me. Anyways, I’m certainly delighted I found it and I’ll be
bookmarking it and checking back often!
I do not even know how I ended up here, but I thought this post was great.
I don’t know who you are but definitely you’re going to a famous blogger if you are not already 😉 Cheers!
popular anabolic steroids
References:
https://wspomozycielka-lodz.pl/?p=873
is clear muscle a steroid
References:
https://tuleestudio.com/mostbet-bukmeker-bilan-galabalaringizni-maksimal-darajada-oshirish-usullari/
リアルラブドールs mind as she stood open-mouthed,listening to us both.
セクシー えろIn my soul and in my heart,I’m convinced I’m wrong!”“That’s very strange! I cannot make it out.
Due To This Fact, it’s typically avoided by steroid customers who choose to go for lighter steroids, which may still yield impressive results (such as testosterone or Dianabol). The above unwanted effects, plus the reality that Sustanon 250 is an injectable steroid, can end result in some individuals avoiding this anabolic steroid. Testo-Max solves all of those problems, so it’s understandable why this authorized steroid is extremely coveted. D-Bal was formulated by Loopy Bulk to duplicate Dianabol’s constructive effects however with out the antagonistic results. This allows bodybuilders to remain wholesome while building muscle, as a substitute of destroying their health in the short or long run. Anavar is by far the most well-tolerated steroid for females, unlike Winstrol. Oral Winstrol continues to be thought of a comparatively gentle steroid in comparison with most others.
The main reason people take anabolic steroids is to construct muscle dimension and power. In this text, we reveal the most effective steroids for mass and the dosages utilized by bodybuilders right now. It can take up to 4 months to revive pure testosterone levels after being on anabolic steroids for an extended time. Often often identified as efficiency and picture enhancing medication, anabolic steroids are synthetic medication that imitate male intercourse hormones (testosterone), and are used to develop and restore muscle tissue. We see such stacks resulting in further mass and strength gains, but additionally increased unwanted effects. Stacking a quantity of steroids collectively will exacerbate testosterone suppression, ldl cholesterol values, and blood strain. All anabolic steroids will suppress endogenous testosterone production.
Females looking at utilizing Winstrol often wish to use it for bulking, chopping, and/or contest prep. Like Anavar, females shall be very aware of Winny’s anabolic results, leading to substantial muscle development (if the food plan supports it). Women will virtually exclusively use Winstrol in oral type solely as a outcome of only very low doses are used, and this has a half-life of about 9 hours.
Another indicator of dependence is withdrawal once anabolic steroid use stops 42. Withdrawal signs can embrace fatigue, restlessness, lack of appetite, insomnia, reduced sex drive, and steroid cravings forty four. The most dangerous of the anabolic steroid withdrawal signs is depression, because it sometimes leads to suicide makes an attempt 45.
With scientific studies sometimes utilizing doses of 150mg per day or even more, we all know it’s attainable to use Anadrol at these dosage levels. If you’re a person who responds poorly to Anadrol (whether it’s water retention, cholesterol, or your liver), then 150mg may be difficult to tolerate. We can have a glance at medically prescribed dosages of Anadrol to see its power17. When used for muscle losing conditions, Anadrol is often prescribed at just 2.5mg per day. Issues like water retention should be virtually non-existent, and stress on the liver and cardiovascular system must be significantly decreased. Steroid medicines are man-made and are similar to the natural hormones made in the physique.
The downside of Anavar is that it is extremely costly, due to the issue in manufacturing this compound and excessive demand. Therefore, the monetary price of experiencing average features could be very high. Deca Durabolin is a popular injectable bulking steroid, sometimes used within the off-season.
However, not all folks respond the identical (just like with anabolic steroids), so some folks can make more gains than others. A person’s training and food plan are additionally essential in determining outcomes. Sustanon 250 is an efficient testosterone ester utilized in bulking cycles to add significant amounts of muscle and power. Some imagine Sustanon 250 to be one of the best type of testosterone as a outcome of it containing each short and lengthy esters. Sometimes, we see Sutanon 250 produce exceptional ends in the early and latter phases of a cycle. Simply prior to the ban on steroids within the Olympics, the German Democratic Republic (GDR) began a program with the targets of synthesizing new anabolic steroids for his or her athletes to use in various sports activities. Their body of research remains the most intensive assortment of data on using steroids in athletes ever complied (5).
If you raise weights or you’re on the bodybuilding scene, you’ve nearly certainly heard of Anavar. This is certainly one of the most-talked about steroids and is whispered about in numerous gyms everywhere in the world. When your physique uses saved vitality, it’s going to burn the sugars and fat you’ve saved. Anabolic steroids are categorised as controlled substances in many countries as a result of their potential for misuse and abuse. In the Usa, they are classified as Schedule III medicine underneath the Managed Substances Act. SARMs carry out the very same task as Steroids, by binding to the Androgen receptor by which a protracted chain of occasions take place and you finish up with increased muscle and elevated bone density.
It is C-17 alpha alkylated to be able to enable for oral administration, and a substitution of its second carbon atom with an oxygen atom, granting it stronger anabolic capabilities. In comparison with Testosterone, studies have demonstrated Anavar to have a minimum of three occasions and a maximum of 6 instances the energy of Testosterone[2]. As there’s an elevated risk of duodenal ulcers and abdomen ulcers, medical advice must be sought if indigestion, acid reflux or tummy (abdominal) pains occur. For individuals vulnerable to these circumstances, treatment may be prescribed to minimize back the signs and the danger of creating an ulcer. Steroid medicines (sometimes referred to as corticosteroids) are man-made (synthetic) variations of steroid hormones produced by the body. Dianabol isn’t an acceptable steroid for females to use because of its potency, which results in severe virilizing effects.
References:
https://pedselite.com/bygg-storre-ben-forvandla-kycklingbenen-till-tradstammar/99736/
Only the hooked up ester differs, controlling the release rate of the hormone. Both are very related, however Testosterone Cypionate has a slightly longer half-life of one additional day. At the sensible degree, users are unlikely to note a difference, and the choice often comes right down to availability.
You can have a glance at T3 and insulin for the more hardcore, however provided that you realize what you’re doing with those compounds. You won’t be as involved about utilizing ancillary compounds throughout these short cycles, however if you want to go ahead with some, you’ll take a glance at the same compounds mentioned for the other longer cycles. In my opinion, it’s greatest to make use of Anavar in milder cycles where you’ll have the ability to reduce suppression while maintaining your features.
So, it is important to study steroid energetic half-life earlier than utilizing them. If they use any powerful anabolic steroids, they will face strong masculine or virilization effects. So, it is advisable to make use of gentle steroid merchandise to get a lean and hard physique with none virilization symptoms. All of the above steroid merchandise are relatively mild and really helpful for female customers. It’s the metabolites – the remnants of the metabolized anabolic steroids – that you just won’t have any idea are there until you’ve been tested.
The use of HDL-cholesterol boosting supplements, similar to niacin, could additionally result in underestimating risk when utilizing algorithms based on HDL-cholesterol. Thus it is very important inquire about complement use in this group of sufferers. If pharmacological intervention is indicated, statins are the first-line of treatment to decrease LDL-cholesterol. Statins may trigger muscle pain in a small proportion of users (152), but this aspect effect might happen more regularly in those who engage in regular intense exercise (153). For this group of sufferers, an skilled panel recommends using hydrophilic statins (rosuvastatin and pravastatin) at a low-to-moderate dose, as hydrophilic statins are regarded as extra hepatoselective (153). If the statin is not tolerated, it’s advisable to change to a lipophilic statin (e.g. simvastatin or atorvastatin), reduce the dose, or try an alternate-day routine (154). If regardless of these attempts statin intolerance stays a difficulty, other pharmacological options, such as ezetimibe or proprotein convertase subtilisin/kexin type 9 (PCSK9) inhibitors, should be explored.
It is feasible that the higher dosages used, use of various AAS, or different methods used to measure CEC (which is not standardized), may underlie these differences. While it remains to be determined if and to what extent an AAS-induced increment in blood stress increases CVD danger, it appears prudent to discourage use when an AAS consumer meets the standards for hypertension. If a affected person continues utilizing AAS long-term nonetheless, treatment seems sensible.
Regardless, persistent AAS-induced hypogonadism has been reported within the literature in a number of instances (65, 178). Future analysis is needed to delineate the AAS cycle options or affected person characteristics that hinder recovery and end in partially reversed, prolonged, or persistent hypogonadism. The testicular manufacturing of testosterone is governed by the hypothalamic–pituitary–gonadal axis (HPGA; see Figure 5). Gonadotropin-releasing hormone (GnRH) neurons of the hypothalamus secrete GnRH in pulsatile style into capillaries of the hypophyseal portal system. GnRH binds to its receptor, the GnRH receptor, on gonadotrophic cells of the anterior pituitary. Activating this G protein-coupled receptor triggers a cascade of occasions that stimulates the synthesis and release of luteinizing hormone (LH) and follicle-stimulating hormone (FSH).
A post cycle therapy plan or “PCT”, it’s a phrase that’s often thrown round inappropriately on many steroid message boards. In many cases, people count on way an extreme amount of out of publish cycle remedy, and others won’t give it an opportunity based on a lack of understanding. With this in thoughts, we need to explain the purpose of publish cycle therapy, what you presumably can actually anticipate and the finest way to implement it. Additional, we want to discuss when it should be implemented; in some circumstances, a PCT plan shall be followed when it shouldn’t have been; don’t fear, it will all make sense. Dr. O’Connor has over 20 years of experience treating men and women with a historical past of anabolic steroid, SARM, and PED use.
So once again, when using a 19-Nor steroid, you must prioritize the control of prolactin, and you’ll then make this facet impact one that might be avoided. Stick to the dosages above when using as much as 200mg of Nandrolone weekly, but contemplate growing your dopamine agonist dose at higher steroid doses. Increased estrogen just isn’t more doubtless to trigger these stereotypical steroid-induced anger and aggression issues. Instead, you’re more more doubtless to see changes regarding melancholy or lethargy – that is one thing to significantly consider as properly if you have existing mental health issues. This is another reason why stopping estrogen levels from growing too much is essential, together with all of the bodily unwanted effects.
References:
https://pedselite.com/sustanon-250/32430/
A healthcare skilled can monitor your bodily and mental health, adjusting dosages and awaiting warning indicators of psychological distress. Talking of melancholy, it’s a common unwelcome guest within the steroid user’s psyche. The synthetic highs induced by these substances can result in crushing lows when the effects put on off or when use is discontinued. It’s like your brain’s reward system has been so overstimulated that it struggles to search out pleasure in on a regular basis life. And let’s not overlook about anxiety – that fixed companion that whispers doubts and fears, even as your muscles grow stronger. In the Usa, you need a prescription to get any anabolic https://pedselite.com/did-arnold-schwarzenegger-use-steroids/13492/. Anabolic steroids are substances which would possibly be just like the hormone testosterone.
All Estrogens are synthesized through aromatization by way of the aromatase enzyme. With the aromatase enzyme being the enzyme responsible for the manufacturing of Estrogen in both men and women, we will see how this pertains very importantly to the anabolic steroid person shortly. Steroids work by appearing on androgen receptors which boosts muscle growth. For instance, oxandrolone and testosterone cypionate deal with primary hypogonadism and some breast cancers. Over time, these substances have gone via completely different ranges of acceptance and guidelines. Kaufman, M. J., Janes, A. C., Hudson, J. I., Brennan, B. P., Kanayama, G., Kerrigan, A. R., … & Pope, H. G. Mind and cognition abnormalities in long-term anabolic-androgenic steroid users.
Wanting ahead, bodybuilding wants open talks amongst medical doctors, regulators, and athletes. As the sport changes, understanding steroids absolutely is key to preserving everyone healthy and the sport clear. Some steroids, like dromostanolone, have robust anabolic and anti-estrogenic properties. They show the careful steadiness between gaining muscle and avoiding unwanted effects. The central nervous system (CNS) feels the effects of steroids in many ways. Trying to the longer term, there’s still a lot to be taught about the long-term psychological results of steroid use. As research continues, we could achieve new insights into the method to higher manage and mitigate these effects.
By growing protein synthesis, steroids promote the growth and restore of muscle tissue, leading to a rise in muscle mass. Steroids, a term that holds both awe and controversy on the earth of sports activities. For a long time, athletes from varied disciplines have turned to the use of steroids to spice up their athletic efficiency. Steroids, also referred to as anabolic-androgenic steroids (AAS), are synthetic substances that mimic the results of the male hormone testosterone within the body. Despite their popularity for enhancing muscle development, their use in sports activities has been a topic of debate because of their potential dangers and illegal standing in many professional sports.
Tetrahydrogestrinone (THG) is one other designer steroid that was specifically manufactured so it might not be detected in doping checks. The U.S. Meals and Drug Administration (FDA) banned the sale of THG in 2003, declaring that it was not a complement as marketed but quite a PED with a possible for abuse and well being hazards. “Stacking” refers to using several different sorts of steroids on the similar time. “Pyramiding,” in the meantime, refers to the practice of slowly rising the quantity, dose, or frequency of steroids to achieve a certain peak, after which the quantity and frequency are steadily tapered down. Our writers and reviewers are experienced professionals in medicine, habit remedy, and healthcare.
Anabolic steroids administration may be by way of oral pills, injections, lotions or topical gels, and skin patches. Anabolic steroids can also be used for other situations as decided by your doctor. You might have the ability to avoid mouth and throat irritation if you gargle and rinse your mouth with water after each puff in your corticosteroid inhaler. Some researchers assume that inhaled corticosteroid medication could gradual progress rates in children who use them for asthma. Corticosteroid medicines are used to deal with rheumatoid arthritis, inflammatory bowel illness (IBD), bronchial asthma, allergic reactions and lots of other conditions.
Whereas not as potent as anabolic steroids, authorized steroid alternate options can nonetheless provide significant advantages for individuals looking to improve their athletic efficiency or physique. It is important to notice that these dietary supplements should be used along side a healthy diet and exercise routine for optimum outcomes. Oxymetholone is used medically to deal with osteoporosis, anemia, and losing syndrome. It is also used as an AA steroid by bodybuilders for its capacity to boost muscle growth and energy by increasing testosterone levels. Anadrol additionally improves recovery and stamina by reducing or delaying fatigue due to increased purple blood cell production, which offers extra oxygen to the muscle tissue. Its use as a treatment for anemia is a testament to its capacity to enhance pink blood cell rely. The misuse of anabolic steroids and different performance-enhancing medication (PEDs) poses serious health risks, together with melancholy, liver injury, stroke, and heart assault, which may have an result on an athlete’s quality of life long-term.
To get one of the best from Primobolan, you do should take greater doses, and this, in fact, pushes the price up additional. One of the large causes Deca is added to a long cycle is its distinctive advantages to the joints and bones, providing essential help when great stress is being positioned on the joints and bones over many months. Joint and bone help could be why some people add Deca to a long cycle as a secondary compound. Negative libido impacts are potential; dosage is commonly set at half of the testosterone dose to fight this. In my experience, these cycles have their place, BUT you better have a good cause for eager to go in this direction because it won’t be with out its downsides. Frontloading Testosterone Enanthate can get your blood plasma ranges up to 500mg much faster.
There are a lot of reasons women choose to not use steroids to boost their physique or increase efficiency. Females who use steroids are at risk of considerable physiological adjustments. This is the pure consequence of placing much larger quantities of testosterone or related male hormones into the feminine physique. Standard steroid cycles are often the place to begin for brand spanking new customers however are additionally a staple in the strategy of experienced bodybuilders. The outcomes achieved over a 10–12-week normal cycle can be incredible (provided you’re employed onerous in the gym). It’s also not an awesome length of time to decide to using steroids.
While anabolic steroids have their place in the therapy of certain medical circumstances, these medicines usually are not protected for any other use. Any guarantees of higher athletic efficiency are additionally not backed by medical evidence. The stimulative results of trenbolone could also be attributed to declines in mental well being. This typically interprets to a short-term enhance in dopamine and adrenaline levels for the primary few weeks and then significantly less dopamine from there onward. Our patients usually report preliminary euphoria at the start of trenbolone cycles after which a crash toward the top.
Some AAS customers would possibly, therefore, resort to the use of hCG or human menopausal gonadotropin (hMG) to keep up testis quantity quite than in search of to protect fertility per se. Whether Or Not or not AAS are ultimately found to impair kidney perform, long-term use resulting in (untreated) hypertension is most likely to inflict renal damage. Biochemically, this expresses itself in relatively small elevations of blood aspartate aminotransferase (AST), alanine aminotransferase (ALT), lactate dehydrogenase (LDH) and gamma-glutamyl transpeptidase (GGT) (99) values. Not Often, AAS-induced hepatotoxicity might manifest itself in jaundice and pruritus (100, 101).
Understanding the side effects of steroids is essential for athletes and bodybuilders. Many are tempted by the promise of speedy muscle development, but the long-term health prices are important. It’s necessary to weigh the short-term benefits in opposition to the long-term dangers. Steroids are sometimes used by bodybuilders and athletes to increase muscle mass and improve performance. Nonetheless, steroids come with many unwanted effects that may have an result on both bodily and mental health. These anabolic steroids also produce milder unwanted facet effects in comparability to trenbolone, in our experience. For more info on appropriate anabolic steroids for girls, learn this article, which references relevant medical analysis and offers dosing pointers.
Girls treated with testosterone for breast cancer require monitoring for indicators of virilization. The root cause of gynecomastia is hormonal, ensuing from an imbalance of androgenic and estrogenic action on breast tissue (201). Extra particularly, gynecomastia results from an absolute or relative deficiency of androgenic, or absolute or relative excess of estrogenic, action on breast tissue. A number of conditions that affect the levels or actions of these intercourse hormones can due to this fact trigger gynecomastia. Not surprisingly, gynecomastia is a facet impact that can occur on account of AAS use.
These modifications are normally identical to the identical changes in pubescent males. If anabolic steroid use is not halted, the progress of those adjustments may be such that a distinct male-like voice by means of pitch and tone can totally develop. This includes clitoromegaly (growth of the clitoris) in a female fetus, as properly as pseudohermaphroditism (the simultaneous growth of male and female sex organs in the fetus). The use (or even direct contact) with anabolic steroid products of any type ought to be avoided in any respect prices by pregnant females.
Many believe they are a quick repair for muscle acquire, overlooking the potential dangers. This misunderstanding can lead to poor choices and well being consequences. Anabolic steroids are manufactured drugs that replicate the consequences of the male hormone testosterone.
The body’s testosterone levels will rise when first taking Dianabol, as a outcome of it basically being exogenous testosterone. However, the physique will acknowledge that testosterone ranges are excessively excessive, and thus, in a bid https://pedselite.com/byg-storre-ben-forvandl-kyllingebenene-til-traestammer/99726/ take care of homeostasis, it’ll shut down pure testosterone production through the testes (17, 18). It does this by inhibiting the HPT (hypothalamic-pituitary-testicular) axis. The liver is a resilient organ with sturdy self-healing properties (commonly regenerating itself post-cycle).
Tren Ace is strong and works shortly, however at the same time, will probably be pretty suppressive even during this short-term use. So, to make use of Tren Ace in this cycle, it’s recommended to add HCG at a low dose of round 500iu weekly (split into two administrations per week). This means such a short cycle shall be favored by folks with particular causes to run a cycle of this size rather than a normal one. As I’ve already detailed, blasting for measurement and power is almost similar to utilizing Anadrol or Dianabol as a kickstart in longer cycles. What may change is your coaching and diet to tweak the outcomes based on personal objectives.
It can still trigger liver toxicity, ldl cholesterol imbalances, and testosterone suppression. Women using Anavar would possibly expertise delicate virilization symptoms like voice deepening and elevated body hair. A PCT isn’t needed when taking authorized steroids or steroid alternate options, as they will not shut down women’s natural testosterone manufacturing.
Evidence suggests that weightlifters who misuse anabolic steroids have stiffer tendons, which may result in an increased threat for tendon damage 123. This places these steroid users at risk for acquiring life threatening viral infections, similar to HIV and hepatitis B and C 111. In addition, animal fashions indicate that anabolic steroids suppress the immune system, which could worsen infections 112. In reproductive goal tissues, testosterone may be considered to be a prohormone, being readily converted by 5α-reductase to the more potent androgen dihydrotestosterone (DHT). In different tissues, such as fatty tissue and components of the brain, testosterone is converted by aromatase to the estrogen, estradiol (E2).
Later listed beneath each stimulants and anabolic agents depending on dose and route of administration. This group of gear was first listed within the WADA Prohibited Record in 2004 underneath gene doping or progress components. Zeranol is listed underneath anabolic brokers in the WADA Prohibited Substances Record.
This substance was first listed in the IOC doping list on 1 January 2003 as a diuretic. This substance was first mentioned in WADA tips in 2004 in connection with blood volume expanders and masking methods. This substance was first mentioned in the WADA Prohibited Record in 2004 within the context of plasma growth.
Magnesium helps with ATP production, muscle rest, and sleep high quality. Low sodium levels can result in dizziness, weakness, and poor efficiency. Bodybuilders who sweat closely or comply with low-sodium diets might have to observe consumption intently. As long as you’re dealing with an established brand like Concentrex, one of many Most Trusted Steroid Producers, you have nothing to worry about in regards to the legality and high quality of the product. Although Lixus doesn’t usually sell instantly from its web site, we are ready to affirm that the merchandise offered by their affiliates are legit’.
Though Anavar won’t help customers construct exceptional quantities of muscle, it does have the power to significantly increase power (despite being a chopping steroid). With research reporting trenbolone to be 3x more androgenic than testosterone (12), its vital results on muscular power aren’t surprising. Some of our sufferers report feeling “like the Hulk” on Halotestin, with elevated levels of irritability and anger. Such reactions may be beneficial for workouts; nonetheless, customers ought to be cautious about this steroid negatively affecting their personalities and shut relationships. If somebody is vulnerable to angry outbursts, they should avoid utilizing Halotestin, as it might trigger roid rage. Superdrol is an oral steroid that is a DHT derivative (similar to Anadrol).
The substantial profit is that Dianabol works shortly, and utilizing it initially of a bulking cycle provides the ultimate enhance to your cycle. Many believe they are a fast repair for muscle acquire, overlooking the potential dangers. All of the steroids developed in the course of the steroid increase of the 1950’s and 1960’s could be examined utilizing the Hershberger Assay method.
After injection, an oil depot types inside the muscle tissue and spreads along the muscle fibers – seemingly squeezed between them – forming an elongated form (3). The AAS gradually diffuse out of the oil depot and into the interstitial fluid. The rate at which this occurs strongly is dependent upon the carboxylic acid group that’s connected onto the parent molecule at carbon 17 of the steroid nucleus. This attachment – esterification of the 17β-hydroxyl group – tremendously retards the discharge of the compound from the oil depot by growing its partition coefficient, i.e., making it extra lipophilic and less hydrophilic. Once the esterified steroid molecule reaches the systemic circulation, both via direct diffusion or lymphatic drainage of the interstitial fluid, esterases cleave off the ester group, releasing the father or mother compound (7).
Artificial cathinones, also identified as bath salts, are a category of lab-made stimulants chemically related to substances discovered in the khat plant. Khat is a shrub grown in East Africa and southern Arabia that some folks devour for its stimulant results. Stimulants are a class of medication that enhance the activity of the central nervous system. Sleep drugs are misused when they are taken in a way or dose that’s completely different than prescribed, taken without a prescription, or taken with different medicine to spice up intoxicating results.
References:
https://pedselite.com/arimidex-anastrozole-how-to-use-it-during-steroid-cycles/41817/
Erectile dysfunction may also be a consequence of psychological elements, as libido may rise sharply in an AAS person in the course of the cycle and sometimes hinder a healthy and mutual sexual relationship. There is no good-quality proof indicating that AAS use is damaging to the kidneys. Nonetheless, some findings in the literature point to a potential detrimental effect. In the HAARLEM research, a transient small improve in serum creatinine concentrations of unknown medical relevance was observed throughout AAS use (from 93.1 μmol/L (1.05 mg/dL) to 97.8 μmol/L (1.eleven mg/dL)). Creatinine concentrations returned to baseline after cessation of use. Albuminuria, as measured by dipstick analysis, emerged or elevated in 16% of the themes (155).
So, whereas it’s unnecessary to be a chemistry expert to know that metabolites are a key consider any steroid drug testing, you’ll need to understand how lengthy these metabolites can stay in your system. Testers will normally check for all identified steroids, but when sources are restricted, then solely probably the most generally used steroids will be tested for. As A Outcome Of the testing has to target a particular steroid, the process must include each potential steroid to cowl all bases. However with the popularity of on-line sales, few persons are promoting steroids that means today. You can even lose money if your incoming bundle will get stopped at customs or anywhere else alongside the shipping line earlier than it gets to you.
Our online store supplies detailed product information, really helpful dosages, and safety advice, helping you make informed selections about your well being and health journey. To purchase authentic products, you solely want to choose the proper medication and place an order with us! Original steroids for sale nearly always have an extra protecting capping. The bottle stopper is securely mounted, and subsequently it cannot be opened by hand. The expiration date and batch quantity are all the time printed in a distinct font from the remainder of the inscriptions, and a separate print for the date of manufacture.
Thanks to us you ought to purchase anabolic steroids or auxiliary preparation and make sure of its high quality. GoAnabolics.com doesn’t in any way name for using anabolic steroids, however only provides quality gear for these who decided to use them. Browse now and experience the trusted way to buy steroids online in the USA. We proudly carry Nova Prescribed Drugs steroids, a top-rated model known for lab-tested, performance-driven results.
They constantly monitor all of the achievements in the subject of sports activities pharmacology and, if necessary, with pleasure will prompt you which ones steroids ought to be utilized in every particular case. From testosterone to PCT, our merchandise are manufactured with clinical-grade precision and backed by real efficiency outcomes. Keep In Mind that sustainable outcomes come from consistent coaching, correct diet, adequate restoration, and thoroughly chosen supplements. No matter which path you choose, prioritize your long-term health above short-term gains. Study the necessary thing differences between testosterone esters and Sustanon, their makes use of, benefits, and which one is greatest for your health targets. Discover the newest verified tests confirming the quality and consistency of Dragon Pharma products. Yes-baseline and periodic checks of serum testosterone, haematocrit, liver enzymes and prostate-specific antigen permit clinicians to titrate the dose and detect emerging adverse effects early[1].
At the time, illegal possession and use was punishable by as a lot as one 12 months in prison, and distribution was punishable by up to 5 years prison time. Distribution and possession with the intent to distribute and traffic, particularly to anyone underneath 21 years old, was punishable by as much as 10 years in prison for a primary offense, and up to 30 years for a repeat offense. The legal guidelines since then have modified for the extra severe, imposing much more harsh and draconian penalties that shall be discussed shortly.
These compounds work by growing nitrogen retention and protein synthesis within the muscle, leading to quicker restore and progress after coaching. That’s why they’re so popular in strength sports, physique contests, and even among leisure lifters chasing the next stage of increased muscle mass. But science-backed steroid alternate options, legit peptides, HGH and medically-formulated enhancers do exist, and you will get them legally, together with through buying authorized steroids online, if you understand the place to look.
Protected steroid purchasing in the US isn’t about chasing the bottom price—it’s about deciding on a reputable seller, demanding transparent labeling, and insisting on safe, trackable delivery. Use the guidance above to evaluate distributors and products with a sharper eye, and you’ll scale back danger while maximizing your training outcomes. Nevertheless, users ought to be cautious about using sure authorized steroid manufacturers, as certain firms have been accused of adding unknown substances to their products, leading to authorized action. Authorized steroids, or steroid alternatives, are FDA-approved formulation that mimic the results of anabolic steroids. Ladies need to be very cautious with the anabolic steroids they use, as we’ve found many cause masculinization. For instance, testosterone can enlarge a woman’s clitoris and reduce her breast dimension.
They are on no much less than 5 steroid boards and is the sister web site to the well-known domestic-supply.com. They are the official vendor of Hilma Biocare, Omstal Pharma, Ultima Pharma, and Nakon Medical, and work with them to guarantee you are getting the true products. They also have a warehouse to allow them to ship with lightning-fast velocity. UGfreak.to has been around a little greater than 12 years and is well known on some very large steroid evaluate websites.
Once the steroids are stopped, the physique is now not receiving the synthetic hormones, and the person is left in a state of very low or even no testosterone. It’s critical to bear in mind that it’s not regular for blood to look when you’re injecting steroids into the muscle. If there is any blood if you insert the needle, you hit a vein or artery quite than just muscle tissue. The needle then should be eliminated, and no solution ought to be injected; as a substitute, start again and find a new muscle spot that does not draw any blood. There are three established strategies of administering injections from a medical perspective.
References:
https://pedselite.com/top-3-best-anabolic-steroids/51034/
Steroids, as a broad class, encompass a broad range of compounds with various functions. They may be categorized into a number of varieties, together with corticosteroids, anabolic steroids, and sex steroids. Corticosteroids, particularly, are concerned in regulating various physiological processes, such as immune response, irritation, metabolism, and electrolyte steadiness. They play a crucial function in the body’s response to stress and are often used as drugs to deal with inflammatory situations, allergic reactions, and autoimmune issues.
Irritation (swelling) usually happens when your immune system sends cells to battle infections or heal an harm. Steroids make your body slow down the manufacturing of the chemicals that cause inflammation. When you set a load of exogenous testosterone into your body, you’ll find a way to surpass your normal levels of T. The dose is what’s called supraphysiological, because it can ramp up T ranges way above what your hypothalamus regulates as an upper restrict. As knowing exactly how and where this powerful hormone is produced helps to distinguish it from artificial steroids. They all have their own particular person jobs however work collectively in live performance to optimize both your well being and your physique. Some folks will stop taking steroids without taking any further medications.
Anabolic steroids are not just the steroids in medical use, or steroids that affect metabolism. In truth, some steroids may have a catabolic (muscle and bone wasting) and immune-suppressing activity. Corticosteroids are important, life-saving medication, broadly out there on prescription, they usually share little with anabolic steroids. Androgenic and anabolic substances are steroids that affect the tissues of the body. Androgens promote the development of secondary sex traits in males.
Dianabol raises blood stress like all anabolic steroids, albeit to a extra notable diploma, due to its vast impact on water retention (making blood quantity more and more viscous). For example, some oral types of what’s imagined to be Primobolan have been found to incorporate cheaper compounds similar to Dianabol, which is a considerably stronger steroid. Consequently, the results you expertise will differ significantly from what you anticipate. This can mislead customers into believing that Primobolan is amongst the stronger steroids when, truly, it’s generally thought to be one of many milder options out there. Injectables suppress the hypothalamic-pituitary-gonadal (HPG) axis, similar to orals. Testosterone-based injectables (e.g., Testosterone Enanthate, Testosterone Cypionate) can shut down natural testosterone manufacturing — with suppression persisting for weeks or months relying on ester size and dosage.
Steroids are a class of compounds that every one have an analogous structure and bind to hormone receptors within the body. Anabolic steroids bind to the androgen receptors, whereas corticosteroids bind to the glucocorticoid receptors – leading to completely different results on the physique. When it involves steroids, however, that description is simply one piece of the equation. There are actually a quantity of lessons of steroids, including anabolic steroids and corticosteroids, which have completely different makes use of, side effects, and performance-enhancing qualities. If used correctly and based on the indicated scientific pointers they can be used for the treatment of varied conditions e.g., hypogonadism (anabolic steroids) and asthma (corticosteroids).
Nevertheless, such reductions are often gentle in contrast to other anabolic steroids. Winstrol’s results are similar to Anavar’s, allowing users to cut back fats mass while including average quantities of muscle tissue. The following is a comprehensive list of further anabolic steroid cycles that simultaneously promote muscle hypertrophy and improve fat burning. Deca Durabolin’s weak androgenic nature, when combined with high prolactin ranges, can contribute to circumstances of erectile dysfunction. When androgen levels are insufficient, nitric oxide (NO) concentrations lower. Enough NO manufacturing is important for the provision of blood to the penile tissue. This stack was believed to be one of the distinguished steroid cycles from the Golden Era, thought to have been utilized by Arnold Schwarzenegger and other classic bodybuilders from the Nineteen Seventies.
In most people, an enzyme called 5-alpha reductase within the physique converts a small portion of Testosterone into DHT. Simply like with estrogenic compounds, this distinction in conversion can considerably impression the potency of DHT-based steroids, similar to Masteron. Natural or artificial steroids have garnered significant consideration as a end result of their potential well being results and performance-enhancing properties. Comprehending these compounds’ advantages and potential drawbacks is important for making well-informed selections. While both oral and injectable steroids can ship important gains in measurement, strength, and recovery, their danger profiles differ dramatically — and safety depends on excess of just the method of administration. Most orals suppress natural testosterone production and, in aromatizing compounds, may cause estrogen-related side effects.
Estrogen increases sodium retention, and the anabolic effects mess with protein synthesis in a method that encourages fluid buildup. Each NPP and Deca deliver nandrolone, so their anabolic effects match up. You’ll see similar muscle protein synthesis and nitrogen retention from either one. In phrases of pure muscle tissue being built, trenbolone can rival any bulking steroid. Nonetheless, as a end result of it doesn’t trigger excessive weight achieve because of water loss and fats loss, it takes the 4th spot. Oral steroids stimulate hepatic lipase within the liver, further decreasing high-density lipoprotein (HDL) ldl cholesterol and thus exacerbating blood stress. The aromatizing nature of Dianabol additionally causes water retention, which will increase blood viscosity, decreasing circulation to the heart.
References:
https://pedselite.com/anavar-online-kaufen-7-tipps-um-echte-var-zu-verkaufen/44132/
Im now not positive the place you’re getting your information, however great topic. I must spend some time finding out much more or understanding more. Thanks for magnificent info I was on the lookout for this information for my mission.
hgh cycle bodybuilding
References:
hghx2; https://masajeseroticostarragona.com/author/childoctave47/,
hgh iu dosage
References:
https://skaaning-snider-2.technetbloggers.de/human-progress-hormone-hgh-kaufen
hgh 2 iu per day
References:
how many ml of hgh per day (https://pagesale41.werite.net/anavar-solely-6-weeks-at-seventy-five-mg-ed-outcomes-with-pictures)
hgh 4iu
References:
hgh dosage for anti aging (https://notes.io/ew3NW)
what to stack with hgh
References:
waar staat hgh voor (https://doodleordie.com/profile/musicbeaver87)
interesting facts about steriods
References:
http://everydayfam.com/tauruslatex29/activity/354480/
human growth hormone steroid
References:
https://mes-favoris.top/item/443481
Đến với J88, bạn sẽ được trải nghiệm dịch vụ cá cược chuyên nghiệp cùng hàng ngàn sự kiện khuyến mãi độc quyền.
iwin – nền tảng game bài đổi thưởng uy tín, nơi bạn có thể thử vận may và tận hưởng nhiều tựa game hấp
how much hgh to take a day for bodybuilding
References:
wat betekend hgh (https://sundaynews.info/user/routedate1/)
hgh vor dem schlafen
References:
Hgh Testosteron [https://pad.geolab.space/KwJ4T7TxQxGdLAYUfKUxJw/]
hgh cycle for beginners bodybuilding
References:
Sytropin Hgh Spray (https://schoolido.lu/user/puppyhelmet54/)
hgh ciclo
References:
Hgh Wirkungseintritt Bodybuilding (https://www.blurb.com/user/errorlunch55)
dosage of hgh for bodybuilding
References:
recommended dosage of hgh for bodybuilding (https://www.instructables.com/member/wooltoe4/)
Khám phá thế giới giải trí trực tuyến đỉnh cao tại MM88, nơi mang đến những trải nghiệm cá cược thể thao và casino sống động.
采用高效谷歌站群策略,快速提升网站在搜索引擎中的可见性与权重。谷歌站群
kuwin sở hữu kho game đa dạng từ slot đến trò chơi bài đổi thưởng, mang đến cho bạn những giây phút giải trí tuyệt vời.
利用强大的谷歌蜘蛛池技术,大幅提升网站收录效率与页面抓取频率。谷歌蜘蛛池
kuwin sở hữu kho game đa dạng từ slot đến trò chơi bài đổi thưởng, mang đến cho bạn những giây phút giải trí tuyệt vời.
hgh vorher nachher
References:
hgh dosage, https://pena-middleton-2.hubstack.net/acheter-testosterone-propionate-sp-labs-100-mg-ml-1-flacon-en-france,
how much hgh for bodybuilding
References:
https://prpack.ru/user/indexdonkey4/
hgh cycle before and after
References:
https://pad.stuve.uni-ulm.de/LvfqzCELQtGbf8mcmEuCGA/
Với giao diện mượt mà và ưu đãi hấp dẫn, MM88 là lựa chọn lý tưởng cho các tín đồ giải trí trực tuyến.
2 iu hgh to mg
References:
https://intensedebate.com/people/pondstraw70
I’m not that much of a internet reader to be honest but your blogs really nice, keep it up! I’ll go ahead and bookmark your website to come back later. All the best
iwin – nền tảng game bài đổi thưởng uy tín, nơi bạn có thể thử vận may và tận hưởng nhiều tựa game hấp
Nice read, I just passed this onto a colleague who was doing some research on that. And he just bought me lunch as I found it for him smile So let me rephrase that: Thanks for lunch!
Với giao diện mượt mà và ưu đãi hấp dẫn, MM88 là lựa chọn lý tưởng cho các tín đồ giải trí trực tuyến.
iwin – nền tảng game bài đổi thưởng uy tín, nơi bạn có thể thử vận may và tận hưởng nhiều tựa game hấp
_by this,エッチ コスプレby that_ ?nihilō?,
kuwin sở hữu kho game đa dạng từ slot đến trò chơi bài đổi thưởng, mang đến cho bạn những giây phút giải trí tuyệt vời.
Khám phá thế giới giải trí trực tuyến đỉnh cao tại MM88, nơi mang đến những trải nghiệm cá cược thể thao và casino sống động.
.. Vous n’étiez pas plus près de la SainteVierge,ラブドールpendant les neuf mois qu’elle Vous porta dans son sein,
and he began skipping about the roomand punching himself on the chest.‘What do you scoundrels mean by it?If I’d known about it I should have arrested him!’ Then he ran out,アダルト フィギュア 無 修正
Nice post! Getting the “The disk is write-protected” error when attempting to copy, remove, or format files on a USB device, SD card, or external hard drive? Well, It can happen unexpectedly after carefully removing the device, or even when the drive was working flawlessly just moments ago. This causes uncertainty for many users, particularly if the device contains crucial files, gui format download that must be accessed immediately. Tools such as these can also be helpful when formatting is not possible due to write-protection issues. To get more information, check out the blog.
Good post! Are you Interested in the process of updating NVIDIA GPU drivers? I’ve recommended a useful post that explains it well nvidia gpu drivers . Make sure to restart your computer after installing the drivers to ensure everything runs smoothly. For convenience, the NVIDIA GeForce Experience tool can handle updates automatically. For additional guidance, check out the post.
Thanks for your amazing post. Are you curious about discovering unconscious racial biases? Well, you can use the race purity test to uncover hidden biases and discover how your personal views and presumptions shape your perspective. Explore the site to learn more.
suchdelicate complexions artificially preserved and mended,such gallantswords to look at,コスプレ エロ 画像
Đến với J88, bạn sẽ được trải nghiệm dịch vụ cá cược chuyên nghiệp cùng hàng ngàn sự kiện khuyến mãi độc quyền.
kuwin sở hữu kho game đa dạng từ slot đến trò chơi bài đổi thưởng, mang đến cho bạn những giây phút giải trí tuyệt vời.
hinckley mn casino
References:
https://mapnova.com.co/employer/australian-mobile-casinos-2025-top-mobile-casino-apps/
Đến với J88, bạn sẽ được trải nghiệm dịch vụ cá cược chuyên nghiệp cùng hàng ngàn sự kiện khuyến mãi độc quyền.
iwin – nền tảng game bài đổi thưởng uy tín, nơi bạn có thể thử vận may và tận hưởng nhiều tựa game hấp
フィギュア 無 修正one can’t hold one’s tongue when one has a feeling,a tangiblefeeling,
In unserem aktuellen Casino Test 2025 haben wir zudem das beste Casino in Deutschland gekürt. Wir haben euch die besten Spiele für Spieler in Deutschland gezeigt, mit welcher Zahlungsmethode man Geld auf das Konto einzahlt und was einen Top Casino Bonus ausmacht. Auf unserer Seite habt ihr viel über die besten Online Casinos in Deutschland erfahren. Hier findet ihr eine Liste aller Casino Echtgeldspiele in Deutschland. Hier findet ihr das beste Online Casino für Andoird und iPhone. Das Spielen mit Handy und Tablet hat auch den Casino online Markt in Deutschland erfasst.
Wenn wir hier über die besten und beliebtesten Spiele in Online Casinos Schweiz sprechen, darf Roulette auf keinen Fall fehlen. Kein Wunder also, dass die besten Schweizer Online Casinos auch dieses Kartenspiel in unterschiedlichen Versionen abdecken. Eine Besonderheit der besten Online Live Casinos Schweiz stellen oft die Tischlimits dar. Sie finden klassische Tisch- und Kartenspiele wie Roulette, Blackjack und Poker, aber auch Würfelspiele, Gameshows und Glücksräder. Bei online Slots können Sie schon mit geringen Einsätzen hohe Gewinne erzielen.
References:
https://online-spielhallen.de/casino-bonus-ohne-einzahlung-2025-gratis-no-deposit-boni/
Hi, Neat post. There’s an issue together with your site in web explorer, would test this?K IE nonetheless is the marketplace leader and a good portion of people will leave out your fantastic writing because of this problem.
seminole casino coconut creek
References:
https://maps.google.no/url?q=https://levine-zimmermann-3.technetbloggers.de/accommodation-in-casino-nsw
aspers casino newcastle
References:
https://www.google.pt/url?q=https://fancypad.techinc.nl/s/qrTTy9E0-
roulette video
References:
https://maps.google.fr/url?q=https://pittman-rafferty-3.technetbloggers.de/best-online-casinos-in-new-jersey-expert-rankings-of-the-top-spots-to-play-nj-com
casino night fundraiser
References:
https://www.google.ki/url?q=https://postheaven.net/refundwall03/sl-t-pglucky88-casino-brikaarkhrbcchbthukkhwaamt-ngkaar
hitonline
References:
https://maps.google.mw/url?q=https://www.instapaper.com/p/17227872
boulevard casino
References:
https://www.haphong.edu.vn/profile/clevelandeurowen44560/profile
dover downs casino
References:
https://guzhen0552.cn/home.php?mod=space&uid=1732764
genting casino manchester
References:
https://www.google.gr/url?q=https://www.pathofthesage.com/members/francebengal96/activity/670424/
portugues online
References:
https://bookmarkstore.download/story.php?title=best-online-casino-games-2
tropicana casino online
References:
https://vuf.minagricultura.gov.co/Lists/Informacin%20Servicios%20Web/DispForm.aspx?ID=12164421
online casinos australia
References:
https://www.google.com.ai/url?q=https://www.folkd.com/submit/blackcoin.co/the-best-high-roller-lounges-in-australia//
online games play
References:
https://bookmarkfeeds.stream/story.php?title=the-mentalist-las-vegas-tickets-2025-show-schedule-reviews
diamond jo casino dubuque
References:
https://vuf.minagricultura.gov.co/Lists/Informacin%20Servicios%20Web/DispForm.aspx?ID=12166343
winning at roulette
References:
http://1v34.com/space-uid-1180260.html
restomontreal emploi
References:
http://kuniunet.com/home.php?mod=space&uid=2769946
Whats Going down i am new to this, I stumbled upon this I have found It positively helpful and it has helped me out loads. I hope to contribute & assist other customers like its helped me. Good job.
Nice blog! Is your theme custom made or did you download it from somewhere? A theme like yours with a few simple tweeks would really make my blog jump out. Please let me know where you got your design. Thanks a lot
Win789vn8, not gonna lie, it caught my eye. I am trying my luck. See for yourself: win789vn8
Thanks , I’ve just been searching for info about this topic for ages and yours is the greatest I’ve discovered so far. But, what about the conclusion? Are you sure about the source?
銉┿儢銉夈兗銉?銉戙偆銈恒儶theagreement shall be interpreted to make the maximum disclaimer orlimitation permitted by the applicable state law.The invalidity orunenforceability of any provision of this agreement shall not void theremaining provisions.
You are my inhalation, I possess few web logs and very sporadically run out from to post .
Greetings from Colorado! I’m bored to death at work so I decided to check out your website on my iphone during lunch break. I love the knowledge you present here and can’t wait to take a look when I get home. I’m shocked at how fast your blog loaded on my cell phone .. I’m not even using WIFI, just 3G .. Anyhow, great blog!
I got good info from your blog
Goldwin365, huh? I like the sound of that! Who doesn’t want to win gold? Let’s see if goldwin365 lives up to its name. Fingers crossed!
References:
Anavar before after
References:
https://schoolido.lu/user/deadorder00/
References:
50mg anavar before and after
References:
https://able2know.org/user/cobwebelbow64/
Alright, so I stumbled upon nk88bet. It’s kinda basic, not too bad though. It’s alright overall. Have fun: nk88bet
References:
Slot machine odds
References:
http://lideritv.ge/user/spainkarate0/
References:
Online casino slots
References:
https://xypid.win/story.php?title=wd-40-casino-review-evaluation-of-features-and-safety
References:
When should i take anavar before or after workout
References:
https://botdb.win/wiki/Anavar_for_Fat_Loss_Does_it_really_help
References:
Anavar only cycle before and after
References:
https://dokuwiki.stream/wiki/Anavar_kaufen_Sichere_Oxandrolon_Tabletten_online_bestellen
getroids net review
References:
https://bookmarks4.men/story.php?title=a-comprehensive-guide-to-buying-winstrol-ensuring-authenticity-and-quality-products
cheap steroids online
References:
https://xypid.win/story.php?title=herzena-en-costa-rica-donde-comprar-el-producto-original-sus-beneficios-y-consejos-para-autenticidad
taking steroids without working out
References:
https://funsilo.date/wiki/Purchasing_medication_with_a_foreign_prescription_in_Finland
As I website owner I conceive the subject matter here is really great, thanks for your efforts.
most anabolic supplements
References:
https://zenwriting.net/violafield4/analisis-y-comparativa-las-mejores-pastillas-de-testosterona-para-mejorar-tu
how to use steroids safely for bodybuilding
References:
https://smed-sauer-2.mdwrite.net/trenbolon-ist-dieses-anabole-steroid-sicher-zu-verwenden
References:
Casino jack and the united states of money
References:
https://chessdatabase.science/wiki/Jeux_de_plateau_Jouer_en_ligne_sur_Snokido
References:
Europa casino mobile
References:
https://poiskpredkov.by/members/jeansshadow26/activity/507908/
anabolic source
References:
https://ai-db.science/wiki/Comprar_Dianabol_Espaa_HiTech_Mejor_Precio_Farmacia
%random_anchor_text%
References:
https://onlinevetjobs.com/author/capwriter75/
anabolic testerone
References:
https://wifidb.science/wiki/Winstrol_Deutschland_Kaufen_Stanozolol_Ohne_Rezept_Online
%random_anchor_text%
References:
https://imoodle.win/wiki/Glules_minceurs_les_glules_amincissantes_sontelles_vraiment_efficaces
buy steroids in us
References:
https://saveyoursite.date/story.php?title=colombia-archives
supplements to take with steroids
References:
https://xypid.win/story.php?title=testogel-sans-ordonnance-livraison-discrete
natural muscle vs steroids
References:
https://dumpmurphy.us/members/visioncat6/activity/4990/
References:
Silverton casino las vegas
References:
https://bookmark4you.win/story.php?title=get-18-free-up-to-600-welcome-offer
References:
Sloths funny
References:
https://historydb.date/wiki/Paysafecard_Deposit_at_Candy96_Casino_Online_Engagement_for_Australia
References:
Paddy power slots
References:
https://fakenews.win/wiki/Candy96_Australia_Pokies_Bonuses_Fast_PayID_Payouts
References:
Osage casino skiatook
References:
https://hansen-wollesen.hubstack.net/times-tables-game-candy-world
References:
Prairie meadows casino
References:
http://humanlove.stream//index.php?title=kjeldsensahin8509
References:
Roulette betting strategy
References:
https://notes.io/eim6C
References:
Gold country casino oroville ca
References:
http://semdinlitesisat.eskisehirgocukduzeltme.com/user/bodysandra4/
References:
Casino miami jai alai
References:
https://support.mikrodev.com/index.php?qa=user&qa_1=sandratights3
the morestrenuously did she resist his remonstrances.She advanced all thearguments her reason,最 高級 ラブドール
tren results before and after
References:
https://sciencewiki.science/wiki/Trenbolone_Guida_AZ_da_un_bodybuilder_esperto
dmz steroid
References:
https://skitterphoto.com/photographers/2185384/randolph-mathiasen
anabolicsteroidsunleashed
References:
https://funsilo.date/wiki/Winstrol_para_qu_sirve_resultados_y_efectos_secundarios
best way to get cut fast
References:
https://yutoriarukyouikujouken.com:443/index.php?flowerzipper6
References:
Quick hits slot machine
References:
https://case.edu/cgi-bin/newsline.pl?URL=https://online-spielhallen.de/888-casino-aktionscode-ihr-schlussel-zu-exklusiven-vorteilen/
References:
Caesars palace las vegas nv
References:
https://king-wifi.win/wiki/Online_Casinos_Deutschland_Legale_Deutsche_Online_Casinos_TOP5
References:
How slot machines work
References:
https://mapleprimes.com/users/jambangle7
References:
Casino jack
References:
http://techou.jp/index.php?cablecanvas5
References:
Yukon gold casino
References:
https://socialbookmark.stream/story.php?title=24casino-mobile-casino-app-2024-ueberpruefung
References:
Hollywood casino toledo oh
References:
https://images.google.so/url?q=https://online-spielhallen.de/1go-casino-login-ihr-tor-zur-spielwelt/
References:
Casino ct
References:
https://kirkpatrick-bisgaard.thoughtlanes.net/royal-reels-casino-australia-login-to-play-with-royalreels
References:
Mbs casino
References:
https://md.inno3.fr/s/fkTWdQeAq
References:
Riverwind casino norman ok
References:
https://imoodle.win/wiki/Best_Online_Casinos_Accepting_PayID_in_Australia_2026
References:
Lady luck casino las vegas
References:
https://avtovoprosi.ru/user/bombagenda72
with boyish good-nature,offered half his paper,エロ ランジェリー
negative affects of steroids
References:
https://graph.org/How-Low-Testosterone-Affects-Womens-Health-02-04
best muscle growth pills
References:
https://wikimapia.org/external_link?url=https://eecpclinic.com/wp-content/pgs/?integratori_per_dimagrire.html
liquid oral winstrol
References:
https://lynge-morris-2.federatedjournals.com/trenbolone-mix
how do anabolic steroids build muscle
References:
https://dumpmurphy.us/members/litterbeech67/activity/18762/
References:
Maryland live casino reviews
References:
https://long-eriksson-2.thoughtlanes.net/payid-pokies-australia-fast-secure-banking-for-aussie-gamblers
References:
https://blackcoin.co/best-online-casinos-australia-2025-a-comprehensive-guide/
free steroids for muscle growth
References:
https://dreevoo.com/profile.php?pid=1059502
steroids effects on muscles
References:
https://bendtsen-tang-3.blogbright.net/beste-homoopathische-arzneimittel-fur-niedrigen-testosteronspiegel
bulking cycle stack
References:
https://a-taxi.com.ua/user/gumstock1/
expatiated with indications of rapture and delight.This inquiry in a moment blew up that scorching flame which had beenwell-nigh stifled by other necessary avocations.ラブドール 無 修正
anabolic steroids guide
References:
http://premiumdesignsinc.com/forums/user/randomlift4/
best post cycle therapy for steroids
References:
https://bbs.pku.edu.cn/v2/jump-to.php?url=https://serpolicia.es/pages/comprar_dianabol.html
anabolic steroids are a synthetic version of testosterone.
References:
https://ai-db.science/wiki/Ratgeber_Testosteron_steigern_mit_Heilpflanzen_Krutern_und_Lebensmitteln
anabolic steroids test
References:
https://graph.org/Acheter-du-Trenbolone-Injectable-Trenbolone-Injection-en-vente-sur-Lecoq-to-02-05
are steroids legal in the us
References:
https://wikimapia.org/external_link?url=https://www.obekti.bg/sites/artcles/index.php?steroid_cycles_what_are_they.html
pictures of bodybuilders on steroids
References:
https://molchanovonews.ru/user/flowerblue1/
steroid abuse article
References:
https://elearnportal.science/wiki/Les_brleurs_de_graisse_sontils_efficaces
We all react differently to the cocktail of hormones released,so what type of cardio suits each woman will vary.人形 エロ
effects of steroids on females
References:
https://sciencewiki.science/wiki/Appetitzgler_online_kaufen_Sttigungskapseln_HSNstore
steroids before and after
References:
https://sykes-weeks-4.federatedjournals.com/wirkstoff-leptin-appetitzugler-anwendung-wirkung-and-empfehlung
what is steroids
References:
https://classifieds.ocala-news.com/author/flatheron20
anabolic steroids for muscle building
References:
https://buyandsellhair.com/author/slopeperu20/
anabolic steroids body building
References:
https://cameradb.review/wiki/Appetitzgler_Fettbinder_online_kaufen
can you drink alcohol with steroids
References:
https://dempsey-kondrup.federatedjournals.com/8-produits-naturels-approuves-pour-perdre-du-poids
ラブドール 激安andthen goodness knows what will happen! Listen,ll tell you what lldo: Nastasya will stay with him now,
anabolic mass gainer side effects
References:
https://fakenews.win/wiki/Anavar_ProHormone_HiTech_Pharmaceuticals
supplements similar to steroids
References:
https://telegra.ph/Meilleurs-bruleurs-de-graisse-pour-maigrir-efficacement-02-06
side effects of the use of anabolic steroids include which of the following conditions?
References:
https://husted-kelley-3.blogbright.net/27-best-weight-loss-supplements-and-diet-pills-of-2026
tren hair loss
References:
https://rosales-charles-3.technetbloggers.de/anavar-prohormone-hi-tech-pharmaceuticals
oral anabolic steroids for sale
References:
http://dranus.ru/forums/user/thumbrice0/
steroid pills for muscle building
References:
https://prpack.ru/user/coilclimb8/
Goosecap,ラブドール 最 高級I have got children that are asgood men as you,
セックス ドールMaybe you could space it out better?What’s up to all,how is everything,
where to buy steroids reddit
References:
https://fsv-kappelrodeck.de/Home;focus=TKOMSI_com_cm4all_wdn_Flatpress_22523288&frame=TKOMSI_com_cm4all_wdn_Flatpress_22523288?x=entry:entry230425-100332%3Bcomments:1
slot machine sounds
References:
https://www.naturfoto-wittgenstein.de/galleries/alaska-nordkanada/121211-0008_unbenannt/
online roulette play roulette and receive $1500
References:
https://fcla.de/NEWS/index.php/;focus=STRATP_com_cm4all_wdn_Flatpress_38266970&frame=STRATP_com_cm4all_wdn_Flatpress_38266970?x=entry:entry240831-101233%3Bcomments:1
george thorogood bad to the bone
References:
https://community.decentrixweb.com/index.php/question/ibercaja-14/
puerto rico casinos
References:
http://www.qazaqpen-club.kz/en/user/startcoffee8/
play jacksmith
References:
https://etuitionking.net/forums/users/edgerotate0/
best roulette strategy
References:
https://www.marocbikhir.com/user/profile/577925
blackjack 2ne1
References:
https://justbookmark.win/story.php?title=online-casino-mit-paypal-sicher-schnell-einzahlen-2026
anabolic oral steroids
References:
https://www.fischereiverein-bopfingen.de/Angelschein-Kompaktkurs-Ostalb;focus=TKOMSI_com_cm4all_wdn_Flatpress_23711236&path=?x=entry:entry240227-165953%3Bcomments:1
intertops casino
References:
https://www.youtube.com/redirect?q=https://free100pokiesnodeposit.blackcoin.co
shokawah casino
References:
https://www.alldriver.ir/user/washermale21/
wheeling island casino
References:
https://decker-enevoldsen.thoughtlanes.net/crypto-gaming-and-instant-withdrawals
macau casinos
References:
https://www.24propertyinspain.com/user/profile/1382630
majestic pines casino
References:
https://freebookmarkstore.win/story.php?title=instant-casino-mobile-app-instant-auf-handy-spielen
Your place is valueble for me. Thanks!…
mac online backup
References:
http://downarchive.org/user/erafight5/
tropez casino
References:
https://prpack.ru/user/limitshop3/
royal vegas flash casino
References:
https://hikvisiondb.webcam/wiki/CryptoFriendly_Gaming_Experience_With_NoRules_Bonuses
king neptunes casino
References:
http://jobs.emiogp.com/author/asianail6/
kahneeta casino
References:
https://bom.so/Os8wG2
european roulette
References:
http://amur.1gb.ua/user/marketsleet17/
bet365 mobile casino
References:
http://bioimagingcore.be/q2a/user/marketbell42
marksville la casino
References:
https://school-of-safety-russia.ru/user/frenchseal92/
red hawk casino
References:
https://cattletrailers.com.au/author/eventrange18/
mono wind casino
References:
https://livebookmark.stream/story.php?title=galaxy96aus-reviews-read-customer-service-reviews-of-galaxy96aus-com
sacramento casinos
References:
https://medibang.com/author/27854771/
32red mobile casino
References:
https://instapages.stream/story.php?title=contact-us-online-play-environment-for-australia
the lodge casino
References:
https://socialbookmarknew.win/story.php?title=mastering-fast-payments-and-live-dealer-action-at-casino-kings-mentorifi
us online casinos
References:
http://jobs.emiogp.com/author/porchclient57/
mahnomen casino
References:
http://uvs2.net/index.php/user/chancecare34
gold eagle casino
References:
https://myenglishguide.com/members/jumpercousin84/activity/22775/
hard rock casino tulsa ok
References:
http://kriminal-ohlyad.com.ua/user/kendomagic03/
jacks or better strategy
References:
https://cognos.space/alzheimer-previna-se-sem-remedios/
woodbine casino
References:
http://styx.funsite.cz/index.php/book
steroid side effects for men
References:
http://kriminal-ohlyad.com.ua/user/shellhill2/
%random_anchor_text%
References:
https://atesoglusogutma.com/user/helenlisa5/
%random_anchor_text%
References:
https://zenwriting.net/peruvirgo3/jetzt-im-online-shop-kaufen
online casino south africa
References:
https://ontariowi.com/village-newsletter/
%random_anchor_text%
References:
https://www.mixcloud.com/effectisland6/
%random_anchor_text%
References:
https://prosmart.by/user/walrusknee4/
casino cleveland ohio
References:
https://www.simplywired.co.uk/category/blog/
natural prednisone
References:
http://csmouse.com/user/bongosprout4/
common steroid
References:
https://egamersbox.com/cool/index.php?page=user&action=pub_profile&id=328867
no deposit roulette
References:
https://windows7obraz.com/16-usb-windows-7-live-cd-zagruzochnaja-s-fleshki.html
pink floyd pompeii
References:
https://suzavci.com/cijena-suzavca-koliko-kosta-i-sto-stvarno-dobivate-za-svoj-novac/
casino regina
References:
https://watbosa.ac.th/question/fhhuyyy/
wildhorse casino
References:
https://westerndesertsafari.com/best-2-nzd-deposit-online-casinos-in-nz-2024-172/
river cree casino edmonton
References:
https://watbosa.ac.th/question/oiasjdsds/
casino barriere toulouse
References:
http://yashichi.com/mainimg-1-300×113/
salamanca casino
References:
https://animallovergifts.com/wipes/
slots machines
References:
https://watbosa.ac.th/question/csfgnhiuu/
casino durant ok
References:
http://schlatthof.net/togo-reise-maerz-2020/palmoel-und-seife/
casino shreveport
References:
http://schlatthof.net/togo-reise-herbst-2019/unser-1-tag-in-togo-3fahrt-von-lome-nach-kpalime/
wheel of fortune rules
References:
http://yashichi.com/?p=86
eagle pass casino
References:
https://forum.karnex.in/question/recovery-your-stolen-crypto-btc-usdt-eth-with-the-help-of-trace-hackers-crypto-recovery-447355702876-2/
mobile casino action
References:
https://www.bonbini-na-curacao.nl/cropped-seru-coral-logo-5-png/
century casino cripple creek
References:
https://www.elsieisy.com/aicha-blogfest/
gaming club casino
References:
https://vietex.blog.fc2.com/blog-entry-549.html
32red mobile casino
References:
https://legal-immobilier.fr/optimiser-la-rentabilite-de-son-bien-locatif/
scioto downs casino
References:
https://www.elsieisy.com/ladies-skirts/
no download casino
References:
https://animallovergifts.com/dogtoys/
sands regency casino reno nv
References:
http://schlatthof.net/togo-reise-maerz-2023/die-maerz-reise-2023-geht-los/
casinos san diego
References:
https://www.elsieisy.com/raped/
oroville casino
References:
https://www.realitateavalceana.ro/planul-jude%c8%9bean-de-incluziune-sociala-2026/
casino palm springs
References:
http://kupe.aetutw.org/modules/tadnews/index.php?ncsn=6&nsn=561
don johnson blackjack
References:
https://vivek-desai.com/shortcodes/image-teasers/
orlando casino
References:
https://vietlinklogistics.com/gioi-thieu/tam-nhin-su-menh.html
hard rock casino tampa florida
References:
https://www.elsieisy.com/apatt-remembering-africas-true-patriots-in-a-time-of-moral-poverty/
à cause de l’amour que nous portons et devons porter ànous-mêmes et à tous les hommes; à cause aussi de l’amour que nousportons à Jésus et du souvenir de Ses douleurs; à cause du désir quenous devons avoir de la justice,c’est-à-dire de la gloire de Dieu et dela peine que nous devons éprouver en voyant l’injustice,ラブドール
la riviera casino
References:
https://cpdbouvxc3m7.blog.fc2.com/blog-entry-295.html
indianapolis casino
References:
http://www.upendogroup.ngdafrica.com/spip.php?article56
missouri casinos
References:
https://forum.karnex.in/?show=answers
gamehouse casino
References:
http://schlatthof.net/togo-reise-herbst-2019/schwitzen-in-der-kara-region/
isle casino
References:
https://community.decentrixweb.com/index.php/question/lewiscrila-8/
rivers casino
References:
https://animallovergifts.com/catloversgift/
william hill android app
References:
https://magiamgia.blog.fc2.com/blog-entry-48494.html
cripple creek casinos
References:
https://wspomozycielka-lodz.pl/?p=907
memphis casinos
References:
http://schlatthof.net/togo-reise-november-2023/es-geht-gleich-in-die-vollen-uns-erster-tag-in-togo/
california indian casinos
References:
https://www.niconya.com/start-page.html
craps board
References:
https://royaltech.ng/2024/04/25/the-evolution-of-smart-home-electrical-systems-for-everyone/
suncoast casino las vegas
References:
https://www.elsieisy.com/the-look/
I have been told theycould.和服 エロI don’t know by experience,
pros and cons of taking steroids
References:
https://peatix.com/user/29015226
supplements to build muscle fast gnc
References:
https://humanlove.stream/wiki/Testostrone_en_pharmacie_notre_avis_1_alternative
steroids vs non steroids
References:
https://intensedebate.com/people/topsquash7
steroids medication names
References:
https://dreevoo.com/profile.php?pid=1186201
sam e long term use
References:
https://onlinevetjobs.com/author/repaironion4/
anabolic supplements that work
References:
https://securityheaders.com/?q=https://thehollywoodtrainerclub.com/static/pgs/?buy_clenbuterol_4.html
best steroids to get ripped
References:
http://09vodostok.ru/user/waydance4/
muscle works supplements
References:
https://waywoman3.bravejournal.net/buy-clenbuterol-usa-legal-clenbuterol-for-sale-online
can you get big without steroids
References:
https://lovewiki.faith/wiki/Clenbuterol_for_Weight_Loss_Does_It_Work
craze supplement for sale
References:
https://hikvisiondb.webcam/wiki/Sopharma_Clenbuterol_20mcg_Tablets_Fat_Burning_Cutting_Support
References:
Parx casino
References:
https://www.elsieisy.com/4-steps-avoiding-quarrels-relationship/quarrelling-couple/
References:
Maryland live casino
References:
https://ohkimslaw.com/media-report/?bmode=view&idx=9100094
m’aimer,créature si pauvre hélas! simaligne,ラブドール
References:
Video poker download
References:
https://medibang.com/author/27974734/
References:
Best online casino games
References:
https://raindrop.io/niccomic0/ottosenadler8259-68541251
References:
Le manoir richelieu
References:
https://graph.org/No-Verification-Withdrawal-Casinos-Australia-2026-Instant-Payouts-Guide-03-17
References:
Live roulette online
References:
https://linkvault.win/story.php?title=225-up-to-10000-180fs-across-3-first-deposits
References:
Mississippi casinos
References:
https://fravito.fr/user/profile/2214569
References:
Grand casino gulfport
References:
https://peatix.com/user/29182728
Philanthropic people lose all sense of humanity.ラブドール 販売It is theirdistinguishing characteristic.
References:
Deca steroids side effects
References:
https://git.secretserver.club/kennycilley980
References:
I want steroids
References:
https://gitea.b54.co/leandranacht0/www.canadiannewcomerjobs.ca9199/wiki/Dianabol-and-Winstrol-Cycle%3A-Dosage%2C-Benefits%2C-and-Side-Effects
References:
R/steroids
References:
http://49.234.27.222:3000/leonelkesteven/leonel2019/wiki/Legal-Dianabol-Tablets-for-Women-Before-and-After-Results
References:
Tren for cutting
References:
http://72.60.136.153/@louellaclever
References:
D ball steroid side effects
References:
http://dibodating.com/@vaniaannis0271
References:
How do you take anabolic steroids
References:
https://florencemasebe.co.za/Khadzi-s-Diary/index.php/,focus=AFRIHP_com_cm4all_wdn_Flatpress_2557736&path=&frame=AFRIHP_com_cm4all_wdn_Flatpress_2557736;focus=AFRIHP_com_cm4all_wdn_Flatpress_2557736&path=?x=entry:entry160518-165338%3Bcomments:1
References:
Hgh spray gnc
References:
https://uxofuciw.myhostpoint.ch/Startseite/index.php/;focus=HSTPTP_com_cm4all_wdn_Flatpress_10103534&path=&frame=HSTPTP_com_cm4all_wdn_Flatpress_10103534?x=entry:entry250214-162126%3Bcomments:1
References:
Define anabolic pathway
References:
https://qflirt.net/@carmelov181123
References:
Why do athletes take anabolic steroids
References:
https://galleryauxburg.com/en/BLOG/index.php/;focus=STRATP_com_cm4all_wdn_Flatpress_51982244&frame=STRATP_com_cm4all_wdn_Flatpress_51982244?x=entry:entry250708-195027%3Bcomments:1
References:
Foods that act like steroids
References:
https://www.ff-garlstorf.de/Startseite;focus=TKOMSI_com_cm4all_wdn_Flatpress_21838727&path=&frame=TKOMSI_com_cm4all_wdn_Flatpress_21838727?x=entry:entry230613-091048%3Bcomments:1
сайт дизайна интерьера квартир услуги дизайнера квартиры
References:
Was arnold schwarzenegger on steroids
References:
https://jasminsideenreich.de/Blog/index.php/;focus=STRATP_com_cm4all_wdn_Flatpress_7099662&path=&frame=STRATP_com_cm4all_wdn_Flatpress_7099662?x=entry:entry231129-152426%3Bcomments:1
References:
Medical uses of steroids
References:
https://www.rbconsulting.info/MEDIEN-BLOG/BLOG/index.php/;focus=HSTPTP_com_cm4all_wdn_Flatpress_6899652&frame=HSTPTP_com_cm4all_wdn_Flatpress_6899652?x=entry:entry210302-234514%3Bcomments:1
References:
Steroid side effects long term
References:
https://basement-hamburg.de/Basement/index.php/;focus=STRATP_com_cm4all_wdn_Flatpress_50884589&path=?x=entry:entry250104-131630;comments:1
Zahnprobleme? sparen mit dentaltourismus zahnbehandlung im Ausland mit bis zu 70 % Ersparnis. Implantate, Zahnersatz, asthetische Zahnheilkunde und Diagnostik in modernen Kliniken. Wir unterstutzen Sie bei der Wahl des Landes und der Klinik und organisieren Ihre Reise von A bis Z.
dental problems? book your dental holidays today high-quality dental treatment abroad at affordable prices. Implants, veneers, prosthetics, and treatments with a guarantee. We select a clinic, organize your trip, and provide patient support throughout the entire process.
металлический значок ссср изготовление металлических значков на заказ в москве
металлический значок пин https://metallicheskie-znachki213.ru/
значки круглые металлические значки металл срочно москва
печать металлических значков изготовление значков из металла москва
циклевка паркета без пыли цена циклевка паркета недорого
циклевка паркета без пыли спб циклевка паркета
Старый паркет? шлифовка паркета без пыли профессиональное восстановление деревянного пола без пыли и лишних затрат. Удаляем царапины, потемнения и старое покрытие, возвращаем гладкость и естественный цвет. Используем современное оборудование, выполняем циклевку, шлифовку и лакировку паркета под ключ с гарантией качества и точным соблюдением сроков.
Daily Summary: https://dartdocs.app/2026/03/17/noviembre-2025/
Show More: https://archivo.seprin.info/?p=753188
What’s out now: https://allviolinshops.com/the-skill-of-kama-sutra/
Our most valuable: https://www.studiodentalmedica.com/best-of-march-2026/
Go for details: https://www.zimta.org.zw/?p=102144
All the best stuff is here: http://www.eurostarinc.com/jogos-acessivel-nos-casinos-legais-em-portugal/
References:
Best legal supplements
References:
https://peatix.com/user/29219873/view
References:
Are any steroids legal
References:
https://grossman-stensgaard-2.blogbright.net/get-testosterone-prescription-online-1774181457
References:
How to properly use steroids
References:
https://www.svm-tischtennis.de/Nachrichten/index.php/;focus=ALFAHO_com_cm4all_wdn_Flatpress_1989179&path=?x=entry:entry260115-081130%3Bcomments:1
References:
Pci expansion slot
References:
https://bbs.pku.edu.cn/v2/jump-to.php?url=https://de.trustpilot.com/review/hanffidel.de
References:
Pink floyd live in venice
References:
https://bookmarkfeeds.stream/story.php?title=beste-auszahlung-online-casino-top-13-beste-onlinee-casinos-im-februar-2026-graz
References:
Chronic steroid use side effects
References:
http://www.dogpersonality.de/Journal-Club/index.php/;focus=STRATP_com_cm4all_wdn_Flatpress_8672146&path=&frame=STRATP_com_cm4all_wdn_Flatpress_8672146?x=entry:entry190620-130507%3Bcomments:1
Наша лучшая подборка: паркет циклевка метр цена
Обновлено сегодня: шлифовка паркета цена за квадратный метр
References:
Purchase anabolic steroids
References:
https://enouvelles.space/item/594528
References:
Most anabolic steroid
References:
https://md.ctdo.de/s/6XN6SW_R7Z
References:
Steroid online store
References:
https://git.zakum.cn/willgrondin815
References:
Joe rogan steroid
References:
https://martdaarad.com/profile/picsol70615028
References:
Natural bodybuilding supplement stack
References:
https://raimusic.vn/leianewbold686
References:
Cheap steroids pills for sale
References:
http://git.fbonazzi.it/cfxchanel7043
References:
Steroids appearance
References:
https://v.sharevr.com/@nellygjt896036?page=about
References:
D ball steroid for sale
References:
https://pads.zapf.in/s/iA4Ypu0XP9
References:
Steroids names for bodybuilding
References:
http://55x.top:9300/philomenaminni/git.123doit.com2016/wiki/Wirkstoff%3A-Clenbuterol-Unerw%C3%BCnschte-Wirkungen
References:
Inject steroids
References:
https://git.htns.com/harrietttarczy/7422308/wiki/Spiropent-Wirkung%2C-Nebenwirkungen%2C-Dosierung
References:
Women on anabolic steroids
References:
http://49.233.255.41:3000/travisbirdsong
References:
Before and after trenbolone
References:
https://hlumi.com/@tomdaluz76603?page=about
References:
Weightloss steroids
References:
https://tubisocial.com/@bradleyneville?page=about
References:
Pros and cons of taking steroids
References:
https://git.navex.com.br/sherriehollick
References:
Strongest fat burning steroid
References:
https://shop.apexo.in/@angelicalain6?page=about
References:
How to use steroids for bodybuilding
References:
https://www.yalecheung.top:1024/cortezpzh10230
References:
How to start steroids
References:
https://www.oddmate.com/@alicehammond40
References:
How to properly inject steroids
References:
https://git.adityagupta.dev/isaacmenzies79
References:
Winstrol steroid side effects
References:
https://lordhub.vip/lucindagregory
References:
Best muscle building supplement reviews
References:
https://git.automathon.org/jaredpavy0713
References:
How to take steroids for beginners
References:
https://code.ownwire.net/carleybays6088
Играешь на гитаре? аккорды для игры на гитаре большая база аккордов, табулатур и разборов песен. Удобный поиск, схемы аккордов и тексты популярных композиций. Подходит для новичков и опытных гитаристов для обучения и игры.
References:
Cns depressant that was used in body building before it was banned.
References:
https://skitterphoto.com/photographers/2222627/bradford-just
References:
All of the following are common side-effects of ingesting anabolic steroids except:
References:
http://historydb.date/index.php?title=boesenhatch4171
References:
Rol lift.com
References:
https://hedgedoc.eclair.ec-lyon.fr/s/PpllgqZvj
References:
Anadrole amazon
References:
https://hedgedoc.info.uqam.ca/s/r0HClEulv
References:
Muscle stack gnc
References:
https://www.jasminsideenreich.de/Blog/index.php/;focus=STRATP_com_cm4all_wdn_Flatpress_7099662&path=&frame=STRATP_com_cm4all_wdn_Flatpress_7099662?x=entry:entry210626-214845%3Bcomments:1
Нужен займ? быстрый микрозайм взять деньги быстро и без справок. Удобное оформление заявки, быстрые выплаты и минимальные требования. Подберите надежную МФО и получите деньги на карту в короткие сроки.
References:
Buy steroids cycles
References:
https://overby-regan.thoughtlanes.net/dianabol-dbol-the-ultimate-guide
References:
All steroids
References:
http://sc-weiler1946.de/index.php/;focus=STRATP_com_cm4all_wdn_Flatpress_22342930&path=&frame=STRATP_com_cm4all_wdn_Flatpress_22342930?x=entry:entry230320-211356%3Bcomments:1
займ с плохой историей https://tvojbank.ru
References:
Where to buy peds
References:
http://1.13.196.248:3000/irvingcoull007
References:
Usa online casinos
References:
http://kriminal-ohlyad.com.ua/user/epoxyaunt32/
References:
Dianabol steroids for sale
References:
https://incisolutions.app/damiansauceda3
References:
Most powerful steroids
References:
http://8.140.232.131:8100/leomawofford41
References:
Is anadrol a good bulking steroid
References:
https://sithcom.de/linneaborella
Закажите на масло для спецтехники оптом моторное масло в бочках оптом от производителя с доставкой по всей России.
References:
Injectable steroid cycles for sale
References:
https://musixx.smart-und-nett.de/emersontellez9
References:
Proanabolics
References:
http://115.159.194.75:4000/isabellef2765
References:
Best shredding supplement stack
References:
https://tubex.su/@samararaven183?page=about
References:
Beast creatine side effects
References:
https://gitea.wgqcd.com/natishaforney/7838742/wiki/Dianabol-vs-Anavar%3A-Which-Steroid-is-Right-for-You%3F
References:
Play online roulette
References:
https://securityholes.science/wiki/WinSpirit_Casino_AU_2025_Claim_800_AUD_Bonus_250_Free_Spins_Best_Pokies_Online
References:
Buy anabolic steroids online with credit card
References:
https://qarisound.com/alexandramoll8
Tarot readings tarot articles on card meanings, love readings, and daily predictions. Learn how to correctly perform readings and interpret the cards to get accurate answers.
References:
Anadrol and winstrol
References:
http://120.25.164.109:3000/kraigfitzroy04
References:
Da hulk steroids
References:
https://www.workerrenter.pro/profile/shantaefrederi
References:
Pharmacy grade steroids
References:
http://110.42.101.39:13000/krystleakm2978
References:
Best steroid for bodybuilding
References:
https://kayesbamusic.com/chelseapham74
Нужен займ? займ получить взять деньги быстро и без справок. Удобное оформление заявки, быстрые выплаты и минимальные требования. Подберите надежную МФО и получите деньги на карту в короткие сроки.
References:
Testosteron steigern Tabletten
References:
https://boisen-nance-2.blogbright.net/testosteron-produkte-im-uberblick
References:
Cortisol senken Testosteron steigern
References:
https://pads.zapf.in/s/-tWpZIAfyS
References:
Tabletten zur Testosteronsteigerung
References:
https://codimd.communecter.org/_MKABGAaT5aSN-LUA-lYNw/
pin-up скачать бесплатно https://drrebenka.ru
промокод для заказа на алиэкспресс aliexpress промокод на доставку
пин ап казино зеркало пин ап казино вход в личный кабинет
кино 2026 вышедшие смотреть фильмы топ
Volvo в Україні https://spectehnika-volvo.mystrikingly.com/ екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
References:
Steroids to build muscle fast
References:
http://38.47.180.165:3000/aleidasison476/62.234.194.662015/wiki/Health-Information-and-Medical-Information
References:
Safe anabolic steroids
References:
https://git.ewengadonnaud.xyz/florian26x9928/florian2001/wiki/Amazon-com%3A-Irwin-Naturals-Energy-%27%26%27-Endurance-Testosterone-Up-Men-Over-40-60-Sgels-%3A-Health-%26-Household
References:
The best steroid pills
References:
http://81.69.57.215:3000/holliebusey869/8582qflirt.net/wiki/19-Best-Testosterone-Boosters-for-Men-in-2026
References:
Best steroids for weight loss
References:
https://gitea.visoftware.com.co/ralphmcburney
References:
Steriod body
References:
http://49.232.183.190:3000/augustinabello
Volvo спецтехніка https://volvo-2026.carrd.co/ екскаватори, фронтальні навантажувачі та дорожні машини. Надійність, ефективність і сучасні рішення для будівництва. Продаж, підбір і обслуговування техніки для бізнесу.
References:
Buy anavar online usa
References:
https://git.louislabs.com/gerardov976429
References:
What are anabolic steroids side effects
References:
http://47.109.30.152:3000/michellgiron4
References:
Effects of steroids on men
References:
https://empleos.contatech.org/employer/topical-corticosteroids-choice-and-application/
References:
Do steroids make you lose fat
References:
http://20.219.0.85:3000/martahartwick
References:
Steroids to gain muscle mass
References:
https://dimen.krd/@franciscajenyn?page=about
References:
Research chemicals for muscle growth
References:
https://metagap.ro/employer/more-middle-age-men-turn-to-testosterone-for-an-edge/
References:
Steroid alternatives reviews
References:
https://git.source.co.jp/u/berndbeaumont3
References:
Nicknames for anabolic steroids
References:
https://git.0fs.ru/nellybown14300/securityprofinder.com2016/wiki/Sustanon-Gender-Affirming-Hormone-Therapy-Guide-GenderGP
References:
Performance enhancing drugs facts
References:
http://117.72.61.28:5418/mellisacastrej
References:
Anabolic muscle supplements
References:
http://tools.refinecolor.com/loganmurdock57
References:
Is creatine a steriod
References:
http://36.213.200.127:23000/violetmeeson74
References:
Animal test stack
References:
https://koonis.net/margomurry3483
References:
Articles on steroids in sports
References:
https://arabsfans.com/@roxannachamble
References:
Steroids before and after pics after one cycle
References:
http://ng.waemok.co.kr/bbs/board.php?bo_table=faq
References:
Bodybuilders on steroids before and after
References:
https://gitea.mynas-lechner.de/noncorine85845
References:
Pills to grow muscles faster
References:
http://221.203.14.217:3000/noestambaugh82
References:
Muscle mass supplements gnc
References:
https://botdb.win/wiki/User:AndreRascoe75
References:
Crazy mass supplement reviews
References:
http://www.jobteck.co.in/companies/testosterone-matrix-supplement/
References:
Best steroids to burn fat
References:
http://39.99.175.172:8000/nickibellew706